Grafana Enterprise is a critical asset that handles core enterprise monitoring data.
CVE-2025-41115 is a critical vulnerability that allows an attacker to gain administrator privileges with a single HTTP request, without even logging in.
With detailed analysis and proof-of-concept (PoC) techniques already being discussed, exploitation attempts are expected to surge.
Therefore, customers using the platform should prioritize applying security patches and disabling SCIM functionality or strictly restricting external access until the patches are applied.
Our Threat Analysis team continuously monitors vulnerabilities in monitoring and visualization tools and will respond promptly to any related vulnerabilities discovered in the future.
To ensure efficient user management, large-scale organizations leverage the System for Cross-domain Identity Management (SCIM)
protocol to synchronize user information with external Identity Providers (IdPs) such as Okta and Azure AD.
This report provides a technical analysis of CVE-2025-41115, a vulnerability identified in the SCIM provisioning implementation of Grafana Enterprise.
This vulnerability can lead to authentication bypass and privilege escalation and is classified as a severe security issue,
assigned the highest CVSS v3.1 score of 10.0 (Critical).

Source : https://grafana.com/products/enterprise/
The SCIM endpoint in Grafana Enterprise (versions 12.0.x ~ 12.2.x) maps the externalId field sent by an external Identity Provider
to the id (Primary Key, Integer), which is the unique identifier in Grafana's internal database.
Under normal circumstances, the externalId should be managed separately as an external identifier.
However, in vulnerable versions, a critical flaw exists where if an attacker manipulates the externalId value into a numeric string and sends it,
the system misinterprets it as the internal system's unique identifier (id).
Consequently, an attacker, even when unauthenticated or possessing low privileges, can take over an administrator account by sending a specially crafted request to the SCIM API endpoint.
Target Selection: The attacker exploits the fact that the Super Admin account in a Grafana instance typically holds id: 1.
Malicious Request Transmission: The attacker constructs a JSON payload containing the value "1" in the externalId field and sends it to the /api/scim/v2/Users endpoint.
Account Overwriting: While processing this request, Grafana overwrites the information of the Super Admin account (where id = 1) with the email and password supplied by the attacker.
Privilege Acquisition: Subsequently, the attacker can log in using the credentials they configured and gain full system privileges.
Example attack request:
As exploitation attempts in the wild are expected to surge immediately following the disclosure of such a critical vulnerability, it is crucial for organizations operating Grafana Enterprise to immediately implement the following security guidelines.
Immediate Patch Application
Grafana Enterprise must be updated to the latest version (v12.3.0 or higher, or v12.2.1 or higher) to resolve the vulnerability.
Temporary Mitigation (Workaround)
If immediate patching is not feasible, the SCIM functionality must be disabled by setting the enable option in the scim section of the grafana.ini configuration file to false.
Implementing these measures will help prevent potential attacks and strengthen system security.
The MONITORAPP Threat Analysis Team has completed an initial analysis of this vulnerability. The results confirm that effective mitigation is challenging because the exploit requests closely resemble legitimate traffic. Consequently, relying solely on simple pattern signature-based detection methods poses a high risk of false positives.
that enables an attacker to gain Super Administrator privileges with a single HTTP request, without any authentication.
With detailed technical analysis and Proof-of-Concept (PoC) techniques now publicly available, a surge in exploitation attempts in the wild is anticipated.
Consequently, customers using Grafana Enterprise must prioritize applying security patches.
If immediate patching is not feasible, it is essential to disable SCIM functionality or strictly restrict external access.
The MONITORAPP Threat Analysis Team continuously monitors vulnerabilities in monitoring and
visualization tools and is committed to responding promptly to similar vulnerabilities in the future.
https://nvd.nist.gov/vuln/detail/CVE-2025-41115
CVE-2025-41115 is a critical vulnerability that allows an attacker to gain administrator privileges with a single HTTP request, without even logging in.
With detailed analysis and proof-of-concept (PoC) techniques already being discussed, exploitation attempts are expected to surge.
Therefore, customers using the platform should prioritize applying security patches and disabling SCIM functionality or strictly restricting external access until the patches are applied.
Our Threat Analysis team continuously monitors vulnerabilities in monitoring and visualization tools and will respond promptly to any related vulnerabilities discovered in the future.
1. Overview
Grafana Enterprise is the commercial enterprise edition of the world's most widely adopted platform for data visualization and infrastructure monitoring.To ensure efficient user management, large-scale organizations leverage the System for Cross-domain Identity Management (SCIM)
protocol to synchronize user information with external Identity Providers (IdPs) such as Okta and Azure AD.
This report provides a technical analysis of CVE-2025-41115, a vulnerability identified in the SCIM provisioning implementation of Grafana Enterprise.
This vulnerability can lead to authentication bypass and privilege escalation and is classified as a severe security issue,
assigned the highest CVSS v3.1 score of 10.0 (Critical).

Source : https://grafana.com/products/enterprise/
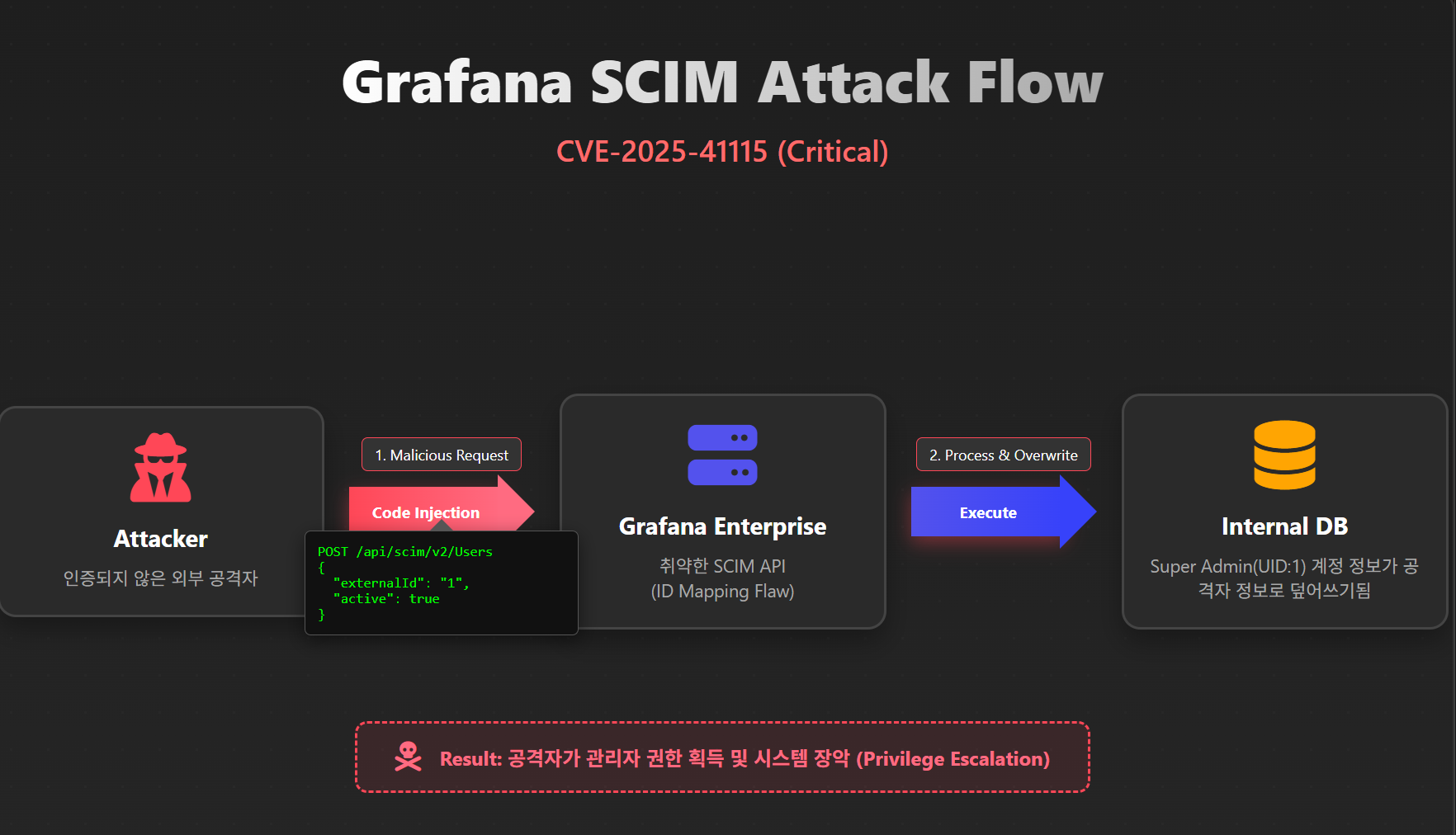
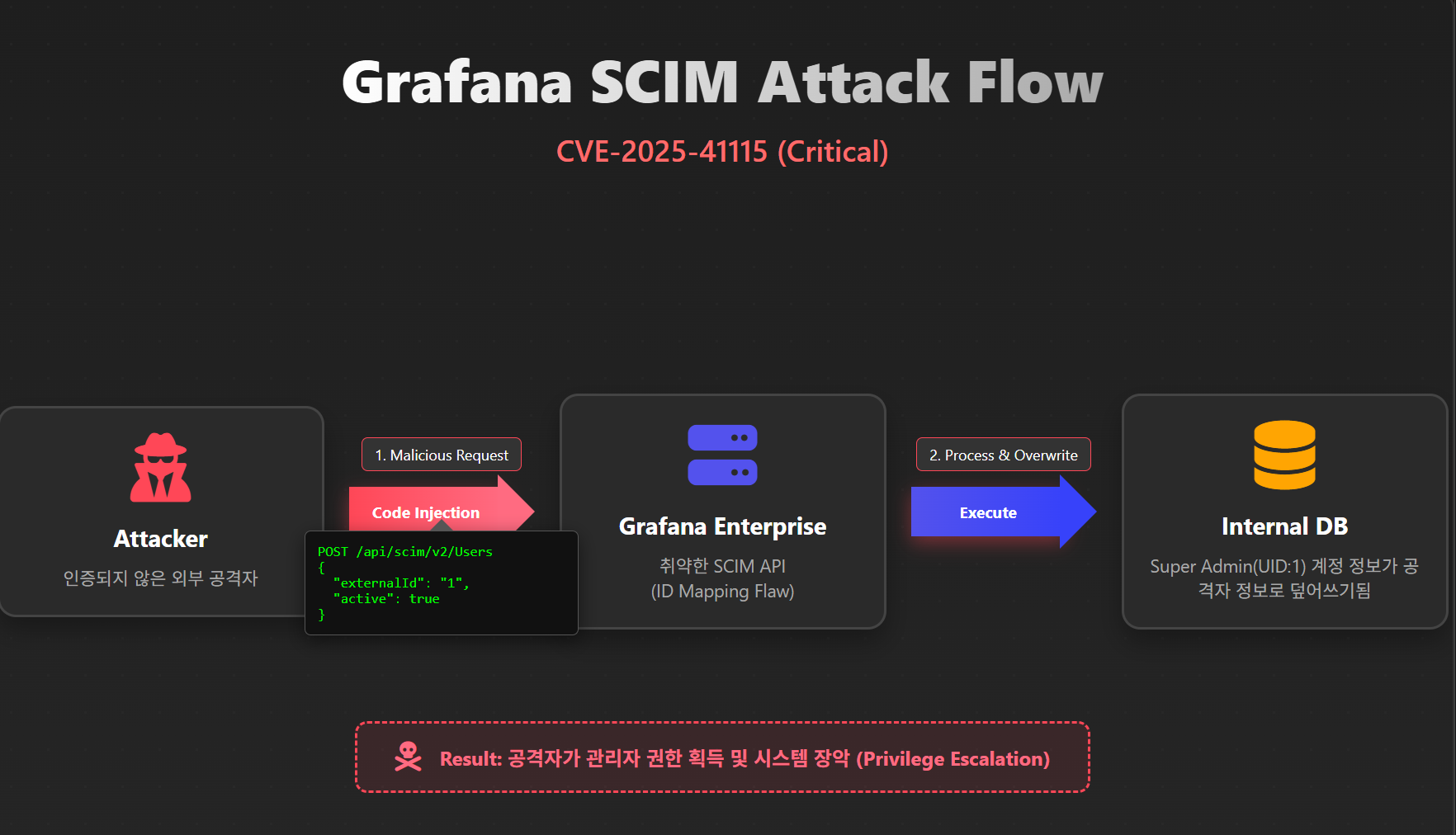
2. Attack type
CVE-2025-41115 stems from an ID Mapping Flaw that occurs when the SCIM API processes user creation and modification requests.The SCIM endpoint in Grafana Enterprise (versions 12.0.x ~ 12.2.x) maps the externalId field sent by an external Identity Provider
to the id (Primary Key, Integer), which is the unique identifier in Grafana's internal database.
Under normal circumstances, the externalId should be managed separately as an external identifier.
However, in vulnerable versions, a critical flaw exists where if an attacker manipulates the externalId value into a numeric string and sends it,
the system misinterprets it as the internal system's unique identifier (id).
Consequently, an attacker, even when unauthenticated or possessing low privileges, can take over an administrator account by sending a specially crafted request to the SCIM API endpoint.
Target Selection: The attacker exploits the fact that the Super Admin account in a Grafana instance typically holds id: 1.
Malicious Request Transmission: The attacker constructs a JSON payload containing the value "1" in the externalId field and sends it to the /api/scim/v2/Users endpoint.
Account Overwriting: While processing this request, Grafana overwrites the information of the Super Admin account (where id = 1) with the email and password supplied by the attacker.
Privilege Acquisition: Subsequently, the attacker can log in using the credentials they configured and gain full system privileges.
Example attack request:
POST /api/scim/v2/Users HTTP/1.1
Host: target-grafana.com
Content-Type: application/json
{
"schemas": ["urn:ietf:params:scim:schemas:core:2.0:User"],
"userName": "attacker@example.com",
"externalId": "1", <-- 핵심 공격 벡터 (관리자 ID '1'을 타겟팅)
"active": true,
"emails": [{
"value": "attacker@example.com",
"primary": true
}]
}
3. Response
The CVE-2025-41115 vulnerability discovered in Grafana Enterprise allows an unauthenticated attacker to hijack administrator privileges via the SCIM API and achieve full system compromise. The severity of this vulnerability is rated extremely high, as it enables the acquisition of the highest privileges remotely without any login process.As exploitation attempts in the wild are expected to surge immediately following the disclosure of such a critical vulnerability, it is crucial for organizations operating Grafana Enterprise to immediately implement the following security guidelines.
Immediate Patch Application
Grafana Enterprise must be updated to the latest version (v12.3.0 or higher, or v12.2.1 or higher) to resolve the vulnerability.
Temporary Mitigation (Workaround)
If immediate patching is not feasible, the SCIM functionality must be disabled by setting the enable option in the scim section of the grafana.ini configuration file to false.
Implementing these measures will help prevent potential attacks and strengthen system security.
The MONITORAPP Threat Analysis Team has completed an initial analysis of this vulnerability. The results confirm that effective mitigation is challenging because the exploit requests closely resemble legitimate traffic. Consequently, relying solely on simple pattern signature-based detection methods poses a high risk of false positives.
4. Conclusion
Grafana Enterprise is a critical asset that manages core enterprise monitoring data. CVE-2025-41115 is a critical vulnerabilitythat enables an attacker to gain Super Administrator privileges with a single HTTP request, without any authentication.
With detailed technical analysis and Proof-of-Concept (PoC) techniques now publicly available, a surge in exploitation attempts in the wild is anticipated.
Consequently, customers using Grafana Enterprise must prioritize applying security patches.
If immediate patching is not feasible, it is essential to disable SCIM functionality or strictly restrict external access.
The MONITORAPP Threat Analysis Team continuously monitors vulnerabilities in monitoring and
visualization tools and is committed to responding promptly to similar vulnerabilities in the future.
5. References
https://github.com/Ashwesker/Blackash-CVE-2025-41115https://nvd.nist.gov/vuln/detail/CVE-2025-41115