A critical vulnerability identified as CVE-2026-21858 (Ni8mare) has been discovered in the open-source workflow automation platform n8n.
Assigned a maximum CVSS score of 10.0, this flaw permits unauthenticated remote code execution (RCE), enabling attackers to fully compromise affected servers.
Although n8n is a popular tool for automation, its footprint is relatively niche compared to ubiquitous web servers like Apache or Nginx.
Consequently, the risk of a widespread internet outage or broad societal impact remains low.
Nevertheless, organizations leveraging n8n for sensitive workflows or internal integrations remain highly vulnerable to targeted attacks.
Administrators are urged to assess the impact and apply mitigation strategies immediately.
Recently, a critical security vulnerability (CVE-2026-21858, Ni8mare) with the maximum CVSS score of 10.0 was discovered in the open-source workflow automation platform n8n.
This vulnerability poses a severe technical risk, allowing attackers to remotely gain full control over affected servers without authentication.
Although n8n is widely used by enterprises and individual developers for workflow automation,
its user base remains relatively limited compared to general-purpose operating systems or web servers (e.g., Apache, Nginx).
Therefore, the likelihood of this vulnerability causing a widespread internet disruption or significant societal impact is considered low.
However, organizations that use n8n to automate sensitive data processing or internal system integrations are at high risk of severe damage in the event of a targeted attack.
It is therefore critical for such organizations to promptly assess their current security posture and implement appropriate protective measures.
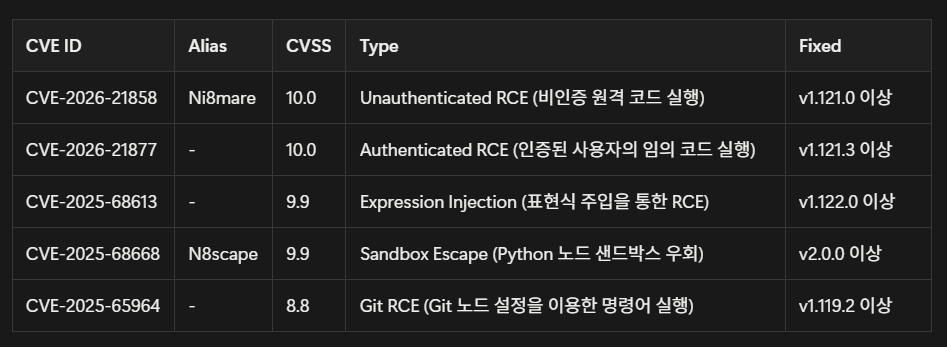
In addition to this issue, several other vulnerabilities have been disclosed.
This report provides a detailed analysis of these vulnerabilities and outlines recommended countermeasures.
This vulnerability occurs in the Webhook processing module of n8n during validation of the received data’s Content-Type.
A flaw in the logic that distinguishes between normal JSON data requests and file upload requests allows attackers
to manipulate headers so that the server misinterprets the request. As a result, external input values can directly affect internal system objects.
CVE-2026-21877
This vulnerability arises when the n8n service handles file uploads from users.
Insufficient restrictions on file formats (extensions and MIME types) enable potentially dangerous files—such as executable scripts—to
be uploaded and stored on the server without any validation, alongside legitimate documents or image files.
CVE-2025-68613 (Expression Injection)
This vulnerability stems from inadequate sandbox isolation within the expression engine used for data processing in n8n workflows.
While JavaScript expressions written by users are intended to execute only within a restricted virtual environment,
a specific bypass technique allows access to core Node.js system objects (e.g., process, require), breaking the expected isolation.
CVE-2025-68668 (N8scape)
This vulnerability results from a sandbox isolation failure within Pyodide—the WebAssembly-based runtime used by n8n to execute Python code.
Although code execution should be confined to a logically isolated environment, an implementation flaw allows internal Python code to escape
the virtual boundary and access the host operating system (Host OS) layer.
CVE-2025-65964
This vulnerability occurs in the Git integration node of n8n. During the processing of user-supplied input (such as repository URLs or commit messages),
inadequate sanitization of special characters can lead to command injection. When Git commands are executed through the system shell,
attackers may craft inputs that cause arbitrary system commands to run.
Basic Information
- Vulnerability Type: Unauthenticated Remote Code Execution (RCE)
- Severity: Critical (CVSS 10.0)
- Affected Versions: v1.65.0 – v1.120.4
- Patched Version: v1.121.0 and above
Root Cause
- This vulnerability originates from insufficient validation of the Content-Type header (Content-Type Confusion) within n8n’s webhook handler, particularly in the parseRequestBody() middleware.
- The system should clearly distinguish between standard data requests (application/json) and file upload requests (multipart/form-data). However, by manipulating the Content-Type header, an attacker can cause the server to misinterpret the request, leading to improper processing.
Attack Flow
1. Context Confusion
- The attacker manipulates the Content-Type header so that a normal JSON data request is processed as a file upload request.
2. Local File Inclusion (LFI)
- During this process, the attacker overwrites the req.body.files object to forcibly read internal files such as configuration (config) files or embedded SQLite database files within n8n.
3. Credential Theft
- From the retrieved files, the attacker extracts administrator credentials or critical secret keys used for session signing.
4. Authentication Bypass and Remote Code Execution (RCE)
- By forging administrator session cookies using the stolen keys, the attacker gains admin privileges without authentication.
- Subsequently, they can use an “Execute Command” node within the workflow to run arbitrary commands on the server (RCE).
Key Threats
- Zero-Click Attack: The attack can be executed with a single HTTP request, even without knowing any usernames or passwords.
- Complete Takeover: Beyond data exposure, this vulnerability can lead to full system compromise, allowing the attacker to obtain root or administrator privileges.
Mitigation Measures
1. Immediate Patching
- The fundamental solution is to upgrade n8n to version v1.121.0 or later (recommended: v1.122.0+). The updated release includes improved validation logic in the parseRequestBody middleware, effectively blocking LFI-based attacks.
2. Key Rotation (Mandatory)
- If a vulnerable version was previously in use, it is highly likely that sensitive keys such as N8N_ENCRYPTION_KEY have already been leaked. Continuing to use old keys after patching may still allow attackers to regain admin access.
- All existing keys must therefore be invalidated, and new keys should be generated and reconfigured.
3. Network Isolation
- If immediate patching is not possible, ensure that the n8n instance is not directly exposed to the public internet.
- Restrict webhook access to trusted IP ranges using Access Control Lists (ACLs) or operate the service within a private VPN network.
4. Web Application Firewall (WAF) Policy
- Deploy WAF rules that detect and block abnormal traffic where the Content-Type header does not match the actual body payload format, thus preventing such exploit attempts.
3-2. CVE-2025-68613: Expression Injection
Basic Information
- Vulnerability Type: Authenticated Remote Code Execution (RCE)
- Severity: Critical (CVSS 9.9)
- Affected Versions: v0.211.0 – v1.120.4 (specific ranges included)
- Patched Version: v1.122.0 and above
Root Cause
- The issue originates from a sandbox isolation failure in the expression engine used within n8n workflows for data transformation and logic execution.
- JavaScript code entered by users should run strictly within an isolated environment, separated from external systems. However, a specific bypass technique allowed direct access to core Node.js system objects such as process and require.
Attack Flow
1. Malicious Code Injection
- An attacker with workflow editing privileges (or a hacker using a compromised account) injects malicious JavaScript code containing a sandbox bypass payload into a node’s parameter input field.
2. Sandbox Escape
- When the workflow is executed and n8n evaluates the expression, the injected payload escapes the logical boundary of the security sandbox and gains access to the host system’s process environment.
3. Remote Command Execution (RCE)
- Once outside the sandbox, the malicious code can invoke the host system shell or establish a reverse shell connection, thereby enabling arbitrary command execution on the underlying operating system.
Key Threats
- Authenticated Threat: Although the attack requires valid login credentials, the protection becomes ineffective in cases of insider threats or compromised accounts.
- Default Credential Risk: If an externally exposed n8n instance uses default credentials (e.g., admin/password) or weak passwords, attackers can easily log in and gain immediate system control.
Mitigation Measures
1. Apply Security Patch (Patch Management)
- Upgrade n8n to version v1.122.0 or later. The latest release strengthens the expression engine’s sandbox mechanism, completely blocking access to risky Node.js built-in objects such as process.
2. Strengthen Account and Access Control (IAM & RBAC)
- Strong Password Policy: Disable default credentials (admin/password) and enforce the use of complex passwords.
- Least Privilege Principle: Restrict workflow creation and modification privileges to trusted administrators only, and assign read-only access to regular users.
3. Restrict Execution of Risky Nodes (Configuration Hardening)
- Disable potentially dangerous nodes capable of executing system commands—such as n8n-nodes-base.executeCommand—by configuring the NODES_EXCLUDE environment variable.
- This limits an attacker’s ability to perform RCE even if an account is compromised.
4. Continuous Monitoring
- Monitor n8n logs for anomalies such as child process creation or suspicious shell command executions (sh, bash, curl, etc.) that may indicate exploitation attempts.
3-3. CVE-2025-68668: N8scape
Basic Information
- Vulnerability Type: Python Sandbox Bypass
- Severity: Critical (CVSS 9.9)
- Affected Versions: v1.0.0 – below v2.0.0
- Patched Version: v2.0.0 and above (introducing the Native Task Runner)
Root Cause
- The vulnerability is caused by a security isolation failure in the Pyodide environment—a WebAssembly-based Python runtime used by the “Python Code Node” in n8n.
- Pyodide is originally designed to run Python code in an isolated environment within a browser or Node.js context; however, a design flaw in n8n’s specific implementation allowed the virtual environment’s restrictions to be bypassed, enabling an escape to the host system.
Attack Flow
1. Malicious Node Setup
- An attacker with workflow editing permissions adds a “Python Code Node” to the workflow.
2. Sandbox Breakout
- The attacker crafts and executes specially manipulated Python code that circumvents Pyodide’s memory and execution restrictions, thereby breaching the sandbox’s logical boundary.
3. Host System Compromise
- Once escaped, the attacker’s code can directly access the host server’s file system, read sensitive files, or manipulate other running processes.
Key Threats
1. Direct Host System Compromise:
- This issue goes beyond application-level compromise. By completely disabling the sandbox barrier, the attacker can directly access and control the operating system’s file system and processes.
2. Privilege Escalation and Data Exfiltration:
- The escaped code inherits the execution privileges of the n8n process (commonly Root in Docker environments or the host user’s privileges in bare-metal deployments). This allows the attacker to steal sensitive server information (e.g., environment variables, SSH keys, database credentials) or even destroy system components.
Mitigation Measures
1. System Upgrade and Architecture Transition (Upgrade to v2.0+)
- Recommended Action: Upgrade n8n to v2.0.0 or later.
- Rationale: Starting with version 2.0, n8n introduces the Native Task Runner architecture, which enforces physical separation between the main process and code execution processes. This design structurally prevents sandbox escapes.
2. Disable Vulnerable Features
- If immediate upgrading is not feasible, the vulnerable Python node functionality should be disabled via environment variables.
- Example configuration: N8N_PYTHON_ENABLED=false (or N8N_DISABLE_PYTHON_NODES=true, depending on the version)
3. Enforce Least Privilege for Containers (Docker Security Hardening)
- Avoid Root Execution: Ensure that n8n does not run with root privileges inside the Docker container. Use PUID/PGID settings or user remapping to restrict container permissions.
- This minimizes impact by preventing attackers from modifying or destroying system-critical files even if the sandbox is bypassed.
This vulnerability allows an attacker to inject malicious JSON data into the req.body.file parameter, potentially leading to the disclosure of internal server files.
While access attempts to common system files such as /etc/passwd can be detected by existing LFI (Local File Inclusion) detection patterns,
access to n8n-specific paths and files—such as /home/node/.n8n/database.sqlite—has been found to result in false negatives, where such activity is not detected by generic patterns.
To address this, a custom detection pattern has been created to identify access attempts to n8n configuration files and database-related extensions (e.g., .sqlite, .config).
However, because successful exploitation of this vulnerability is relatively complex and the practical threat level is assessed to be low, this pattern will not be included in the official pattern update release.
CVE-2025-68613: Expression Injection
This vulnerability is a type of Server-Side Template Injection (SSTI), in which an attacker with a low-privileged account can create a workflow and inject a malicious script
by exploiting insufficient validation of expression input values.
Testing and verification confirmed that such attack attempts are successfully detected and blocked by the existing AIWAF security pattern “2248: JavaScript Server Side Template Injection” (PoC completed).
Therefore, the vulnerability can be mitigated without any additional countermeasures, as the current security policy already provides adequate protection.
CVE-2026-21877: Malware Injection
Although the possibility of malware concealment using the Git Workflow node and the file system has been raised, no concrete exploit code or detailed mechanism has been identified to date.
Accordingly, applying an immediate blocking rule is on hold due to the potential risk of false positives. Continuous monitoring will be maintained,
and an appropriate response policy will be established once more detailed technical analysis becomes available.
https://security.snyk.io/vuln/SNYK-JS-N8N-5518109
https://thehackernews.com/2026/01/critical-n8n-vulnerability-cvss-100.html
https://www.cycognito.com/blog/emerging-threat-cve-2026-21858-cve-2025-68613-cve-2026-21877-n8n-workflow-automation-vulnerabilities/
https://www.sonicwall.com/blog/n8n-ai-workflow-automation-remote-code-execution-vulnerability-cve-2025-68613-
https://www.tenable.com/cve/CVE-2026-21858
https://www.incibe.es/en/incibe-cert/early-warning/vulnerabilities/cve-2025-68613
https://thehackernews.com/2026/01/new-n8n-vulnerability-99-cvss-lets.html
https://www.upwind.io/feed/cve-2026-21858-n8n-unauthenticated-rce
https://github.com/n8n-io/n8n/security
https://zeropath.com/blog/cve-2025-62726-n8n-git-node-rce-summary
https://community.n8n.io/t/vulnerability-issues-on-hosted-version-1-64-1/59587
Assigned a maximum CVSS score of 10.0, this flaw permits unauthenticated remote code execution (RCE), enabling attackers to fully compromise affected servers.
Although n8n is a popular tool for automation, its footprint is relatively niche compared to ubiquitous web servers like Apache or Nginx.
Consequently, the risk of a widespread internet outage or broad societal impact remains low.
Nevertheless, organizations leveraging n8n for sensitive workflows or internal integrations remain highly vulnerable to targeted attacks.
Administrators are urged to assess the impact and apply mitigation strategies immediately.
1. Overview
Analysis of Major Security Vulnerabilities in n8n and Response MeasuresRecently, a critical security vulnerability (CVE-2026-21858, Ni8mare) with the maximum CVSS score of 10.0 was discovered in the open-source workflow automation platform n8n.
This vulnerability poses a severe technical risk, allowing attackers to remotely gain full control over affected servers without authentication.
Although n8n is widely used by enterprises and individual developers for workflow automation,
its user base remains relatively limited compared to general-purpose operating systems or web servers (e.g., Apache, Nginx).
Therefore, the likelihood of this vulnerability causing a widespread internet disruption or significant societal impact is considered low.
However, organizations that use n8n to automate sensitive data processing or internal system integrations are at high risk of severe damage in the event of a targeted attack.
It is therefore critical for such organizations to promptly assess their current security posture and implement appropriate protective measures.
In addition to this issue, several other vulnerabilities have been disclosed.
This report provides a detailed analysis of these vulnerabilities and outlines recommended countermeasures.
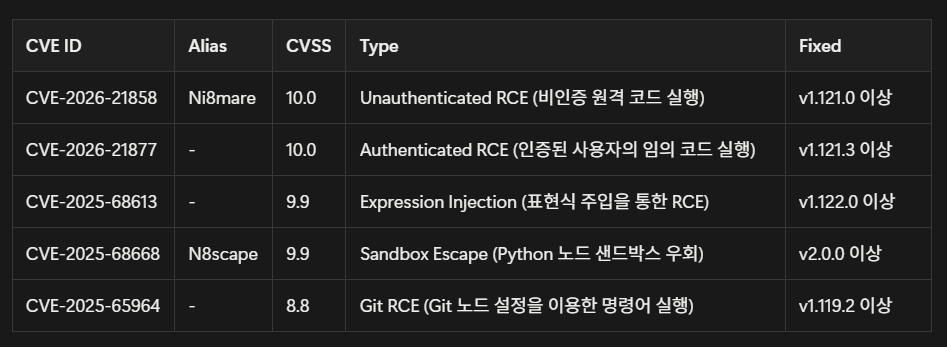
2. Vulneraility
CVE-2026-21858 (Ni8mare)This vulnerability occurs in the Webhook processing module of n8n during validation of the received data’s Content-Type.
A flaw in the logic that distinguishes between normal JSON data requests and file upload requests allows attackers
to manipulate headers so that the server misinterprets the request. As a result, external input values can directly affect internal system objects.
CVE-2026-21877
This vulnerability arises when the n8n service handles file uploads from users.
Insufficient restrictions on file formats (extensions and MIME types) enable potentially dangerous files—such as executable scripts—to
be uploaded and stored on the server without any validation, alongside legitimate documents or image files.
CVE-2025-68613 (Expression Injection)
This vulnerability stems from inadequate sandbox isolation within the expression engine used for data processing in n8n workflows.
While JavaScript expressions written by users are intended to execute only within a restricted virtual environment,
a specific bypass technique allows access to core Node.js system objects (e.g., process, require), breaking the expected isolation.
CVE-2025-68668 (N8scape)
This vulnerability results from a sandbox isolation failure within Pyodide—the WebAssembly-based runtime used by n8n to execute Python code.
Although code execution should be confined to a logically isolated environment, an implementation flaw allows internal Python code to escape
the virtual boundary and access the host operating system (Host OS) layer.
CVE-2025-65964
This vulnerability occurs in the Git integration node of n8n. During the processing of user-supplied input (such as repository URLs or commit messages),
inadequate sanitization of special characters can lead to command injection. When Git commands are executed through the system shell,
attackers may craft inputs that cause arbitrary system commands to run.
3. Analyze
3-1. CVE-2026-21858: Ni8mareBasic Information
- Vulnerability Type: Unauthenticated Remote Code Execution (RCE)
- Severity: Critical (CVSS 10.0)
- Affected Versions: v1.65.0 – v1.120.4
- Patched Version: v1.121.0 and above
Root Cause
- This vulnerability originates from insufficient validation of the Content-Type header (Content-Type Confusion) within n8n’s webhook handler, particularly in the parseRequestBody() middleware.
- The system should clearly distinguish between standard data requests (application/json) and file upload requests (multipart/form-data). However, by manipulating the Content-Type header, an attacker can cause the server to misinterpret the request, leading to improper processing.
Attack Flow
1. Context Confusion
- The attacker manipulates the Content-Type header so that a normal JSON data request is processed as a file upload request.
2. Local File Inclusion (LFI)
- During this process, the attacker overwrites the req.body.files object to forcibly read internal files such as configuration (config) files or embedded SQLite database files within n8n.
3. Credential Theft
- From the retrieved files, the attacker extracts administrator credentials or critical secret keys used for session signing.
4. Authentication Bypass and Remote Code Execution (RCE)
- By forging administrator session cookies using the stolen keys, the attacker gains admin privileges without authentication.
- Subsequently, they can use an “Execute Command” node within the workflow to run arbitrary commands on the server (RCE).
Key Threats
- Zero-Click Attack: The attack can be executed with a single HTTP request, even without knowing any usernames or passwords.
- Complete Takeover: Beyond data exposure, this vulnerability can lead to full system compromise, allowing the attacker to obtain root or administrator privileges.
Mitigation Measures
1. Immediate Patching
- The fundamental solution is to upgrade n8n to version v1.121.0 or later (recommended: v1.122.0+). The updated release includes improved validation logic in the parseRequestBody middleware, effectively blocking LFI-based attacks.
2. Key Rotation (Mandatory)
- If a vulnerable version was previously in use, it is highly likely that sensitive keys such as N8N_ENCRYPTION_KEY have already been leaked. Continuing to use old keys after patching may still allow attackers to regain admin access.
- All existing keys must therefore be invalidated, and new keys should be generated and reconfigured.
3. Network Isolation
- If immediate patching is not possible, ensure that the n8n instance is not directly exposed to the public internet.
- Restrict webhook access to trusted IP ranges using Access Control Lists (ACLs) or operate the service within a private VPN network.
4. Web Application Firewall (WAF) Policy
- Deploy WAF rules that detect and block abnormal traffic where the Content-Type header does not match the actual body payload format, thus preventing such exploit attempts.
3-2. CVE-2025-68613: Expression Injection
Basic Information
- Vulnerability Type: Authenticated Remote Code Execution (RCE)
- Severity: Critical (CVSS 9.9)
- Affected Versions: v0.211.0 – v1.120.4 (specific ranges included)
- Patched Version: v1.122.0 and above
Root Cause
- The issue originates from a sandbox isolation failure in the expression engine used within n8n workflows for data transformation and logic execution.
- JavaScript code entered by users should run strictly within an isolated environment, separated from external systems. However, a specific bypass technique allowed direct access to core Node.js system objects such as process and require.
Attack Flow
1. Malicious Code Injection
- An attacker with workflow editing privileges (or a hacker using a compromised account) injects malicious JavaScript code containing a sandbox bypass payload into a node’s parameter input field.
2. Sandbox Escape
- When the workflow is executed and n8n evaluates the expression, the injected payload escapes the logical boundary of the security sandbox and gains access to the host system’s process environment.
3. Remote Command Execution (RCE)
- Once outside the sandbox, the malicious code can invoke the host system shell or establish a reverse shell connection, thereby enabling arbitrary command execution on the underlying operating system.
Key Threats
- Authenticated Threat: Although the attack requires valid login credentials, the protection becomes ineffective in cases of insider threats or compromised accounts.
- Default Credential Risk: If an externally exposed n8n instance uses default credentials (e.g., admin/password) or weak passwords, attackers can easily log in and gain immediate system control.
Mitigation Measures
1. Apply Security Patch (Patch Management)
- Upgrade n8n to version v1.122.0 or later. The latest release strengthens the expression engine’s sandbox mechanism, completely blocking access to risky Node.js built-in objects such as process.
2. Strengthen Account and Access Control (IAM & RBAC)
- Strong Password Policy: Disable default credentials (admin/password) and enforce the use of complex passwords.
- Least Privilege Principle: Restrict workflow creation and modification privileges to trusted administrators only, and assign read-only access to regular users.
3. Restrict Execution of Risky Nodes (Configuration Hardening)
- Disable potentially dangerous nodes capable of executing system commands—such as n8n-nodes-base.executeCommand—by configuring the NODES_EXCLUDE environment variable.
- This limits an attacker’s ability to perform RCE even if an account is compromised.
4. Continuous Monitoring
- Monitor n8n logs for anomalies such as child process creation or suspicious shell command executions (sh, bash, curl, etc.) that may indicate exploitation attempts.
3-3. CVE-2025-68668: N8scape
Basic Information
- Vulnerability Type: Python Sandbox Bypass
- Severity: Critical (CVSS 9.9)
- Affected Versions: v1.0.0 – below v2.0.0
- Patched Version: v2.0.0 and above (introducing the Native Task Runner)
Root Cause
- The vulnerability is caused by a security isolation failure in the Pyodide environment—a WebAssembly-based Python runtime used by the “Python Code Node” in n8n.
- Pyodide is originally designed to run Python code in an isolated environment within a browser or Node.js context; however, a design flaw in n8n’s specific implementation allowed the virtual environment’s restrictions to be bypassed, enabling an escape to the host system.
Attack Flow
1. Malicious Node Setup
- An attacker with workflow editing permissions adds a “Python Code Node” to the workflow.
2. Sandbox Breakout
- The attacker crafts and executes specially manipulated Python code that circumvents Pyodide’s memory and execution restrictions, thereby breaching the sandbox’s logical boundary.
3. Host System Compromise
- Once escaped, the attacker’s code can directly access the host server’s file system, read sensitive files, or manipulate other running processes.
Key Threats
1. Direct Host System Compromise:
- This issue goes beyond application-level compromise. By completely disabling the sandbox barrier, the attacker can directly access and control the operating system’s file system and processes.
2. Privilege Escalation and Data Exfiltration:
- The escaped code inherits the execution privileges of the n8n process (commonly Root in Docker environments or the host user’s privileges in bare-metal deployments). This allows the attacker to steal sensitive server information (e.g., environment variables, SSH keys, database credentials) or even destroy system components.
Mitigation Measures
1. System Upgrade and Architecture Transition (Upgrade to v2.0+)
- Recommended Action: Upgrade n8n to v2.0.0 or later.
- Rationale: Starting with version 2.0, n8n introduces the Native Task Runner architecture, which enforces physical separation between the main process and code execution processes. This design structurally prevents sandbox escapes.
2. Disable Vulnerable Features
- If immediate upgrading is not feasible, the vulnerable Python node functionality should be disabled via environment variables.
- Example configuration: N8N_PYTHON_ENABLED=false (or N8N_DISABLE_PYTHON_NODES=true, depending on the version)
3. Enforce Least Privilege for Containers (Docker Security Hardening)
- Avoid Root Execution: Ensure that n8n does not run with root privileges inside the Docker container. Use PUID/PGID settings or user remapping to restrict container permissions.
- This minimizes impact by preventing attackers from modifying or destroying system-critical files even if the sandbox is bypassed.
4. Response
CVE-2026-21858: Ni8mareThis vulnerability allows an attacker to inject malicious JSON data into the req.body.file parameter, potentially leading to the disclosure of internal server files.
While access attempts to common system files such as /etc/passwd can be detected by existing LFI (Local File Inclusion) detection patterns,
access to n8n-specific paths and files—such as /home/node/.n8n/database.sqlite—has been found to result in false negatives, where such activity is not detected by generic patterns.
To address this, a custom detection pattern has been created to identify access attempts to n8n configuration files and database-related extensions (e.g., .sqlite, .config).
However, because successful exploitation of this vulnerability is relatively complex and the practical threat level is assessed to be low, this pattern will not be included in the official pattern update release.
CVE-2025-68613: Expression Injection
This vulnerability is a type of Server-Side Template Injection (SSTI), in which an attacker with a low-privileged account can create a workflow and inject a malicious script
by exploiting insufficient validation of expression input values.
Testing and verification confirmed that such attack attempts are successfully detected and blocked by the existing AIWAF security pattern “2248: JavaScript Server Side Template Injection” (PoC completed).
Therefore, the vulnerability can be mitigated without any additional countermeasures, as the current security policy already provides adequate protection.
CVE-2026-21877: Malware Injection
Although the possibility of malware concealment using the Git Workflow node and the file system has been raised, no concrete exploit code or detailed mechanism has been identified to date.
Accordingly, applying an immediate blocking rule is on hold due to the potential risk of false positives. Continuous monitoring will be maintained,
and an appropriate response policy will be established once more detailed technical analysis becomes available.
5. References
https://security.snyk.io/package/npm/n8nhttps://security.snyk.io/vuln/SNYK-JS-N8N-5518109
https://thehackernews.com/2026/01/critical-n8n-vulnerability-cvss-100.html
https://www.cycognito.com/blog/emerging-threat-cve-2026-21858-cve-2025-68613-cve-2026-21877-n8n-workflow-automation-vulnerabilities/
https://www.sonicwall.com/blog/n8n-ai-workflow-automation-remote-code-execution-vulnerability-cve-2025-68613-
https://www.tenable.com/cve/CVE-2026-21858
https://www.incibe.es/en/incibe-cert/early-warning/vulnerabilities/cve-2025-68613
https://thehackernews.com/2026/01/new-n8n-vulnerability-99-cvss-lets.html
https://www.upwind.io/feed/cve-2026-21858-n8n-unauthenticated-rce
https://github.com/n8n-io/n8n/security
https://zeropath.com/blog/cve-2025-62726-n8n-git-node-rce-summary
https://community.n8n.io/t/vulnerability-issues-on-hosted-version-1-64-1/59587