[February 2026 Web Attack Trend Analysis]
1. Weekly Web Attack Trend Analysis
Through weekly web attack trend analysis, it is possible to identify periods during which web attacks werehighly concentrated. These insights can be used to establish proactive prevention and response strategies
in preparation for periods of increased attack activity.
The graph below visualizes the number of web attacks detected by AIWAAP on a weekly basis throughout
January 2026.
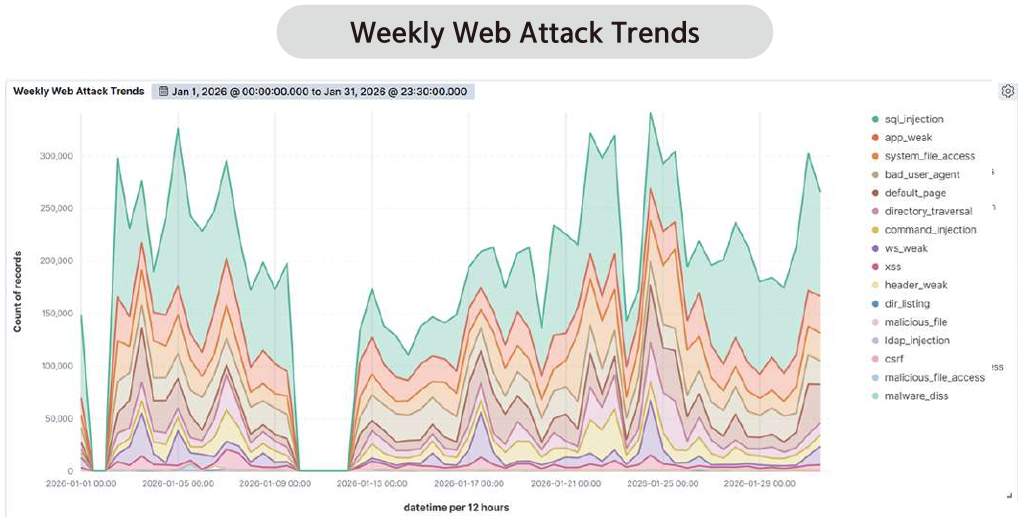
An analysis of the data detected by AIWAAP during January 2026 showed that an average of more than
370,000 web attacks were detected per day. This figure is similar to that of the previous month, indicating
that threats targeting web servers continue to grow in sophistication. In addition, attack frequency was
higher on weekends (Saturday and Sunday) than on weekdays, which can be interpreted as a strategic
approach aimed at periods when web server usage tends to decrease outside regular business hours.
In particular, January 24 recorded the highest concentration of web attacks during the month. Among the
attack types detected on that day, SQL Injection accounted for the largest proportion. SQL Injection is a
representative attack technique that manipulates databases to obtain system privileges or exfiltrate internal
information. Attackers commonly use this method to bypass user authentication mechanisms or to analyze
database structures. Due to these characteristics, organizations must exercise heightened caution in
protecting sensitive information.
In fact, AIWAAP classifies SQL Injection as a high-risk attack type and maintains multiple detection patterns
for it. These findings highlight the need for continuous monitoring and precise response strategies for
major web attack types, including SQL Injection, and will serve as an important foundation for establishing
future detection and blocking policies.
2. Web Attack Trends by Attack Type
By analyzing web attack trends by attack type based on detection logs, it is possible to systematically identify
which types of attacks occurred most frequently over the course of a month. Such analysis goes beyond
simple statistics and serves as a key foundation for establishing organizational security policies and
strengthening response frameworks.
An analysis of the detection logs collected by AIWAAP during January 2026 revealed a wide range of web
attack types. Among them, certain categories exhibited clear patterns, such as being heavily concentrated
during specific periods or accounting for a significant proportion of the total number of attacks. In particular,
classic yet still highly threatening attack types such as SQL Injection and Application Vulnerability ranked
among the most prevalent. These attacks are typically carried out repeatedly using automated attack tools
or botnets.
The graph below visualizes the distribution of web attack types detected by AIWAAP during January 2026.
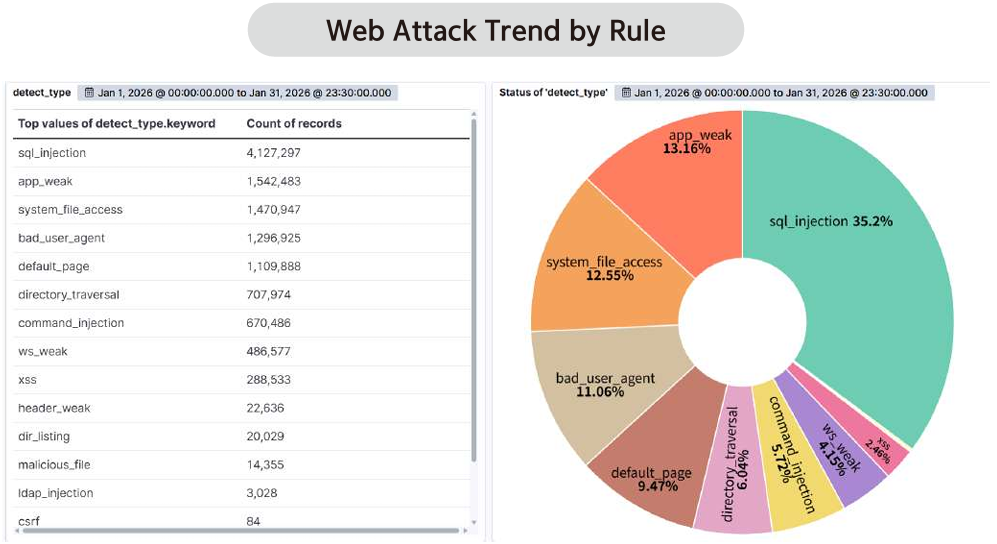
According to statistics on web attack types detected by AIWAAP during January 2026, SQL Injection
accounted for the largest share at 35.2% of total detections. This was followed by App Weakness (13.16%),
System File Access (12.55%), Bad User-Agent (11.06%), and Default Page (9.47%). These results indicate
the need for more precise countermeasures and proactive preventive measures against specific attack types.
First, SQL Injection is a highly critical attack type that consistently ranks near the top of the OWASP Top 10,
and its techniques continue to evolve in diverse and sophisticated ways. This attack typically occurs when
values supplied through user input are directly incorporated into SQL queries and executed. Attackers
exploit this to perform abnormal authentication bypasses, enumerate database structures, and exfiltrate
sensitive data.
In particular, systems that rely on dynamic queries or lack sufficient input validation are highly vulnerable to
such attacks.
The second most prevalent category, App Weakness, refers to attacks that target inherent security flaws
within applications, such as insufficient authentication, weak session management, or configuration errors.
Notably, detections of authentication bypass attempts and API abuse in cloud-based SaaS systems and API
driven services have been increasing. This trend may have implications for the development of future cloud
security policies.
The third most prevalent category, System File Access (12.55%), refers to attempts by attackers to exploit
web application vulnerabilities to gain unauthorized access to internal system files and directories or to
manipulate arbitrary files. Such attacks may arise from improper web server configurations, insufficient
access controls, or failures in directory path validation. If successful, they can lead to privilege escalation or
the installation of backdoors.
The fourth most prevalent category, Bad User-Agent (11.06%), primarily targets requests that use malicious
or abnormal User-Agent strings to probe systems or masquerade as automated scanners or crawlers. During
the reconnaissance phase, abnormal User-Agent strings may reveal clues about the attacker’s tools or
objectives, such as vulnerability scanning, crawling, or scraping, thereby providing indicators for follow-on
attacks. This type of traffic often combines detection evasion techniques (e.g., impersonating legitimate
browsers or using known malicious strings) with large-scale automation, making it difficult to regard as
purely passive. Because such traffic is frequently generated in high volumes by automated scanners, early
detection and blocking are critically important.
The fifth most prevalent category, Default Page (9.47%), targets pages that retain default settings after
installation or system message pages. During the reconnaissance phase, these pages may expose
information about the type and configuration of system software, which can be leveraged for subsequent
attacks. Although generally considered passive in nature, this attack type is often scanned extensively by
automated tools, making early detection and response essential.
The Web Attack Trend Report provides the latest web vulnerability analyses, industry-specific attack patterns,
and key CVE-based vulnerability information, all based on processed data from the AI/ML-powered threat intelligence platform AILabs.
Subscribe to receive the full monthly Web Attack Trend Report!
[ Subscribe → ]