This vulnerability is an authentication bypass and insecure deserialization vulnerability in Fortra GoAnywhere MFT.
An attacker can first obtain the authentication token value through the authentication bypass vulnerability and
then execute serialized malicious code by sending it to a specific endpoint.
A patch for this vulnerability was released in September 2025, and AIWAF products will address this vulnerability through
the "2289 / Fortra GoAnywhere MFT Authentication Bypass (1)" pattern, which will be added in the January 2026 pattern update.
centrally manage all internal and external file transfer processes.
This report provides an analysis and summary of the CVE-2025-10035 vulnerability identified in this solution.

Source : https://www.goanywhere.com/
NVD databases in September 2025. A detailed technical analysis of this vulnerability was published by the watchTowr research team.
The vulnerability allows an attacker to first obtain an authentication token through the authentication bypass weakness and
subsequently execute serialized malicious code by sending it to a specific endpoint.
Authentication Bypass
To perform an insecure deserialization attack, an attacker must first acquire a valid authentication token.
According to the watchTowr team’s analysis, by sending a request containing invalid values to the /goanywhere/license/Unlicensed.xhtml
endpoint and the javax.faces.ViewState parameter, the server responds with an encrypted token value in the Location header’s bundle parameter.
This occurs because when invalid values are submitted, the server attempts to handle the resulting exception using the AdminErrorHandlerServlet.
If the request URL begins with /license/Unlicensed.xhtml, this servlet generates a valid authentication token and associates it with the user session,
allowing an attacker to obtain a legitimate token.
Although the retrieved token value is encrypted, the watchTowr team confirmed that it is encrypted with a hardcoded,
static key found within the internal source code, making it possible for attackers to easily decrypt and obtain the token.
Source : https://labs.watchtowr.com/is-this-bad-this-feels-bad-goanywhere-cve-2025-10035/
Example attack request:
Insecure Deserialization
Subsequently, the attacker attaches the previously obtained token value to the endpoint /goanywhere/lic/accept/—
where the deserialization process takes place—and sends serialized, Java-based malicious code to execute the attack.
However, during the internal deserialization process, a signature verification step is performed. As no method to bypass
this verification has been identified, the precise structure and behavior of the malicious payload remain undetermined.
Example attack request:
bundle=[Malicious Code]
to CISA’s Known Exploited Vulnerabilities (KEV) catalog on September 29, 2025.
Following this, Fortra released a security patch addressing the issue. Customers using the affected product can mitigate
the vulnerability by updating to version 7.8.4 (or Sustain Release 7.6.3) or later.
In our AIWAF solution, this vulnerability will be addressed through the “2289 / Fortra GoAnywhere MFT Authentication Bypass (1)”
pattern, which is scheduled to be included in the January 2026 pattern update.
Source : https://www.fortra.com/security/advisories/product-security/fi-2025-012
The CVE-2025-10035 vulnerability discovered in this product has been assigned the maximum CVSS score of 10.0 and
was promptly added to the CISA KEV catalog, indicating that it is a high-risk security issue. Organizations utilizing
this service are strongly advised to update to the latest version without delay.
Our TA Team continuously monitors vulnerabilities identified in Fortra products and will continue to respond swiftly to
any related security issues discovered in the future.
https://labs.watchtowr.com/is-this-bad-this-feels-bad-goanywhere-cve-2025-10035/
https://www.sonicwall.com/ko-kr/blog/deserialization-leads-to-command-injection-in-goanywhere-mft-cve-2025-10035
An attacker can first obtain the authentication token value through the authentication bypass vulnerability and
then execute serialized malicious code by sending it to a specific endpoint.
A patch for this vulnerability was released in September 2025, and AIWAF products will address this vulnerability through
the "2289 / Fortra GoAnywhere MFT Authentication Bypass (1)" pattern, which will be added in the January 2026 pattern update.
1. Overview
Fortra GoAnywhere MFT is a file transfer solution that enables organizations to securely protect, automate, andcentrally manage all internal and external file transfer processes.
This report provides an analysis and summary of the CVE-2025-10035 vulnerability identified in this solution.

Source : https://www.goanywhere.com/
2. Attack type
CVE-2025-10035 is an authentication bypass and insecure deserialization vulnerability registered in both the CISA KEV andNVD databases in September 2025. A detailed technical analysis of this vulnerability was published by the watchTowr research team.
The vulnerability allows an attacker to first obtain an authentication token through the authentication bypass weakness and
subsequently execute serialized malicious code by sending it to a specific endpoint.
Authentication Bypass
To perform an insecure deserialization attack, an attacker must first acquire a valid authentication token.
According to the watchTowr team’s analysis, by sending a request containing invalid values to the /goanywhere/license/Unlicensed.xhtml
endpoint and the javax.faces.ViewState parameter, the server responds with an encrypted token value in the Location header’s bundle parameter.
This occurs because when invalid values are submitted, the server attempts to handle the resulting exception using the AdminErrorHandlerServlet.
If the request URL begins with /license/Unlicensed.xhtml, this servlet generates a valid authentication token and associates it with the user session,
allowing an attacker to obtain a legitimate token.
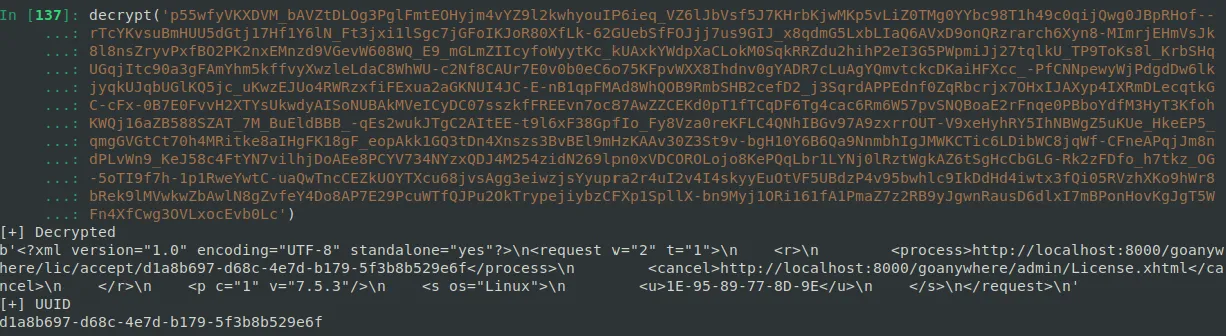
Although the retrieved token value is encrypted, the watchTowr team confirmed that it is encrypted with a hardcoded,
static key found within the internal source code, making it possible for attackers to easily decrypt and obtain the token.
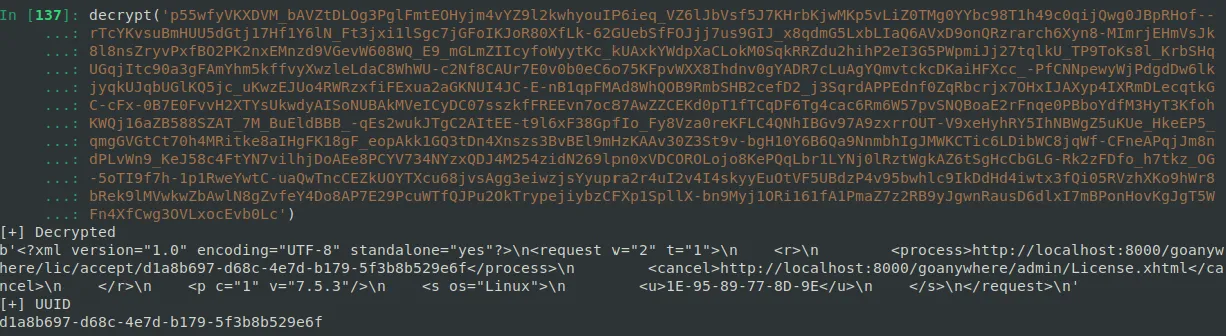
Source : https://labs.watchtowr.com/is-this-bad-this-feels-bad-goanywhere-cve-2025-10035/
Example attack request:
GET /goanywhere/license/Unlicensed.xhtml/test?javax.faces.ViewState=test&GARequestAction=activate HTTP/1.1
Host: www.test.com
Insecure Deserialization
Subsequently, the attacker attaches the previously obtained token value to the endpoint /goanywhere/lic/accept/—
where the deserialization process takes place—and sends serialized, Java-based malicious code to execute the attack.
However, during the internal deserialization process, a signature verification step is performed. As no method to bypass
this verification has been identified, the precise structure and behavior of the malicious payload remain undetermined.
Example attack request:
POST /goanywhere/lic/accept/d1a8b697-d68c-4e7d-b179-5f3b8b529e6f HTTP/1.1
Host: www.test.com
Cookie: ASESSIONID=F970BB906F5F7D325BFC6E261CF87AE6;
Content-Type: application/x-www-form-urlencoded
bundle=[Malicious Code]
3. Response
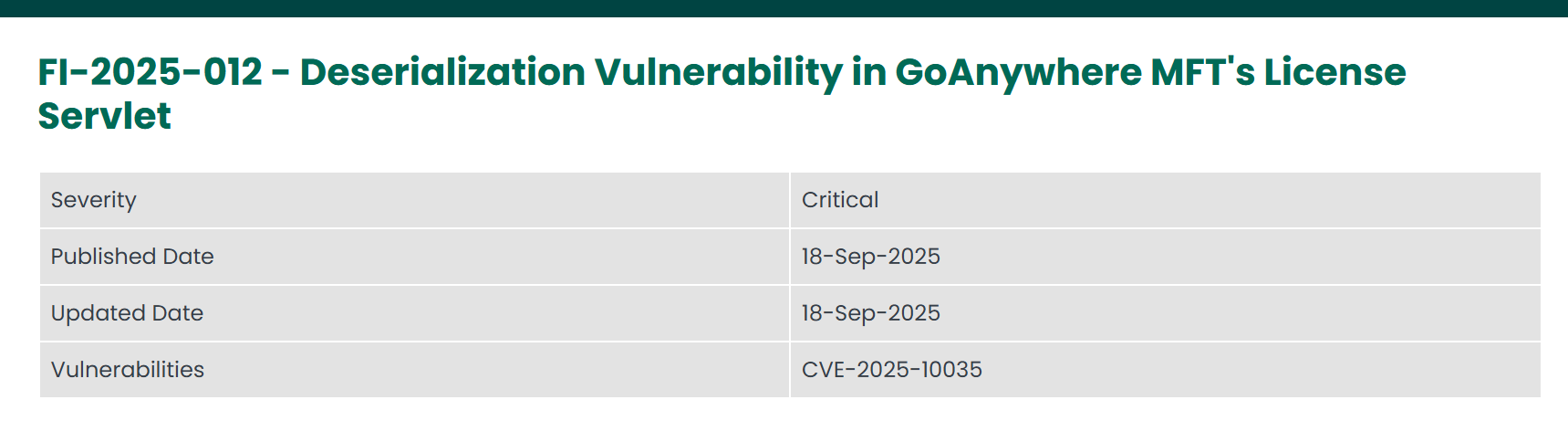
According to CISA, this vulnerability was confirmed to have been exploited by ransomware groups and was subsequently addedto CISA’s Known Exploited Vulnerabilities (KEV) catalog on September 29, 2025.
Following this, Fortra released a security patch addressing the issue. Customers using the affected product can mitigate
the vulnerability by updating to version 7.8.4 (or Sustain Release 7.6.3) or later.
In our AIWAF solution, this vulnerability will be addressed through the “2289 / Fortra GoAnywhere MFT Authentication Bypass (1)”
pattern, which is scheduled to be included in the January 2026 pattern update.
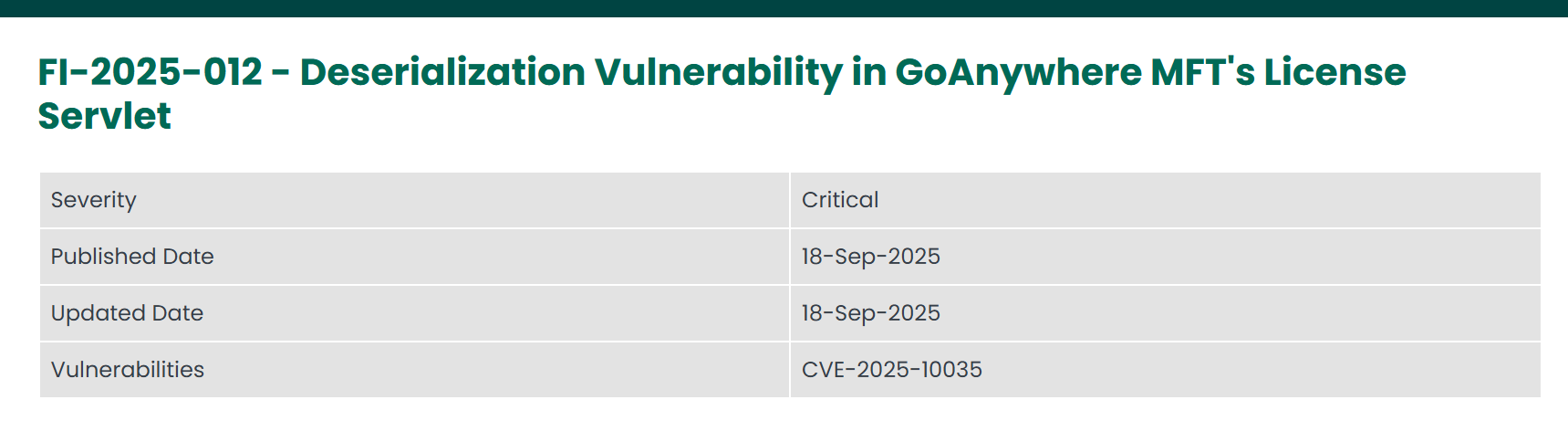
Source : https://www.fortra.com/security/advisories/product-security/fi-2025-012
4. Conclusion
Fortra GoAnywhere MFT is a service designed to securely protect file-sharing processes for enterprise environments.The CVE-2025-10035 vulnerability discovered in this product has been assigned the maximum CVSS score of 10.0 and
was promptly added to the CISA KEV catalog, indicating that it is a high-risk security issue. Organizations utilizing
this service are strongly advised to update to the latest version without delay.
Our TA Team continuously monitors vulnerabilities identified in Fortra products and will continue to respond swiftly to
any related security issues discovered in the future.
5. References
https://nvd.nist.gov/vuln/detail/CVE-2025-10035https://labs.watchtowr.com/is-this-bad-this-feels-bad-goanywhere-cve-2025-10035/
https://www.sonicwall.com/ko-kr/blog/deserialization-leads-to-command-injection-in-goanywhere-mft-cve-2025-10035