Microsoft Office is a critical business asset that handles core documents and data.
CVE-2026-21509 is a critical zero-day vulnerability that allows attackers to gain complete control of a system
by simply opening a manipulated document, directly bypassing built-in security measures.
With confirmed cases of in-the-wild attacks by APT groups already underway, and detailed analysis and
security bypass techniques actively discussed, exploitation attempts are expected to surge.
Therefore, customers using this product line should prioritize applying security patches (out-of-box).
Until the patch is applied, they should either apply temporary mitigations (registry modifications) or
strictly control access to and execution of suspicious documents from outside sources.
Our TA team continuously monitors vulnerabilities in major business software widely used worldwide and
will respond promptly to any related vulnerabilities discovered in the future.
organizations for document creation, data analysis, and communication. To enable seamless document operations and rich content delivery,
Office fundamentally utilizes OLE (Object Linking and Embedding) technology to embed and link data or controls from other applications within documents.
This report provides a technical analysis of CVE-2026-21509, a zero-day vulnerability discovered in the OLE object processing engine and
security mitigation implementation of Microsoft Office. This vulnerability enables arbitrary remote code execution (RCE) by bypassing built-in
security features (such as Kill Bits), has been actively exploited in real-world attacks (in-the-wild) even prior to the official patch release, and
is evaluated as a high-risk security issue with a CVSS v3.1 score of 7.8 (High).

Source : https://thehackernews.com/2026/01/microsoft-issues-emergency-patch-for.html
when Office programs process OLE (Object Linking and Embedding) objects within documents.
The OLE processing engine in Microsoft Office checks security registry settings such as 'Kill Bit' when executing external
objects embedded in documents to block the loading of dangerous COM objects.
In normal logic, malicious scripts or browser controls (e.g., Shell.Explorer.1) should be blocked at this stage,
but vulnerable versions contain a critical flaw that allows attackers to bypass this validation step and forcibly instantiate
objects through specially crafted RTF or Office document structures.
Attackers can execute arbitrary malicious code and seize system control simply by having victims
open manipulated documents (user interaction required), without needing direct system access.
(Note: This vulnerability is not triggered in the Windows Explorer 'Preview Pane'.)
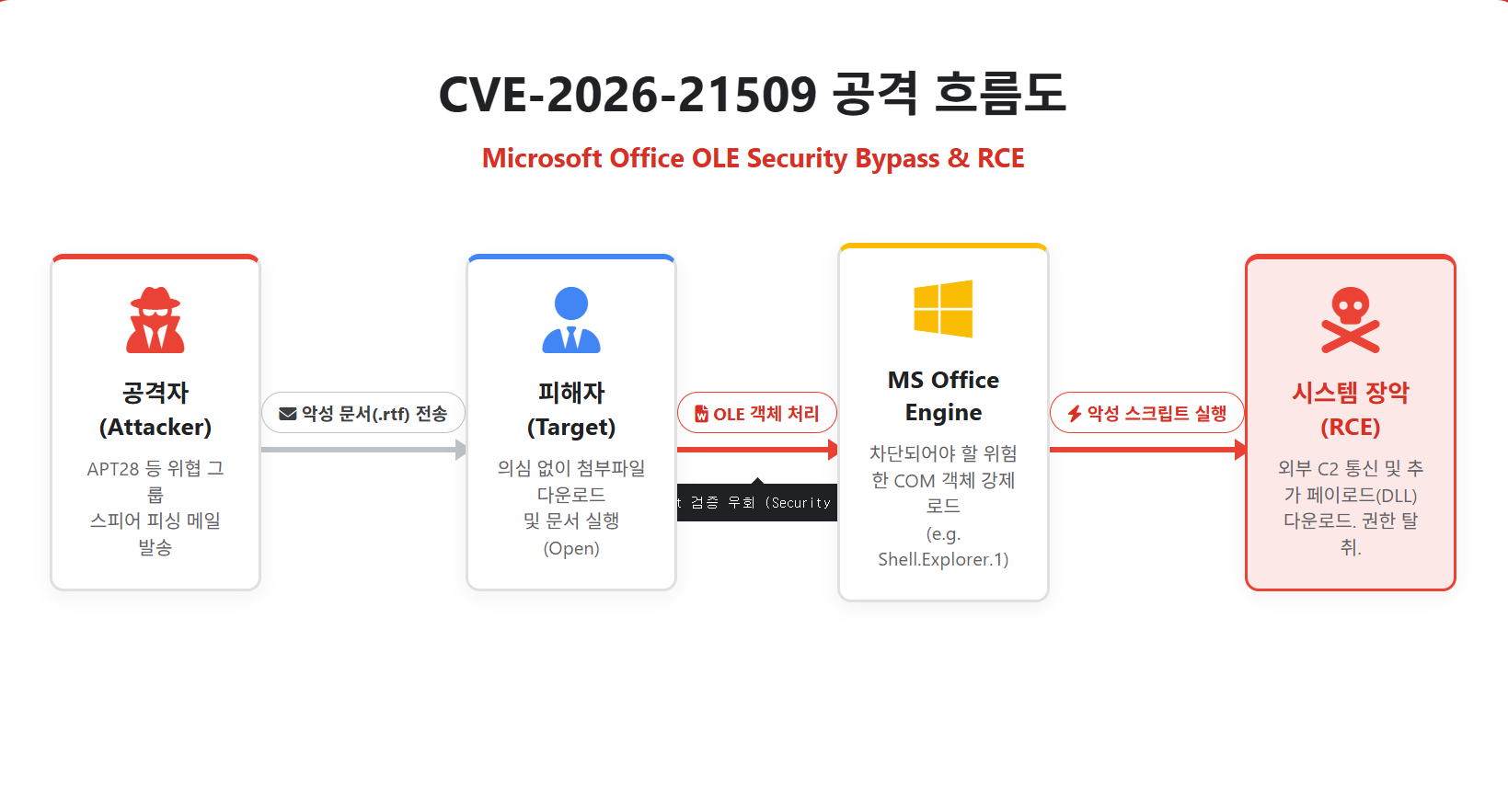
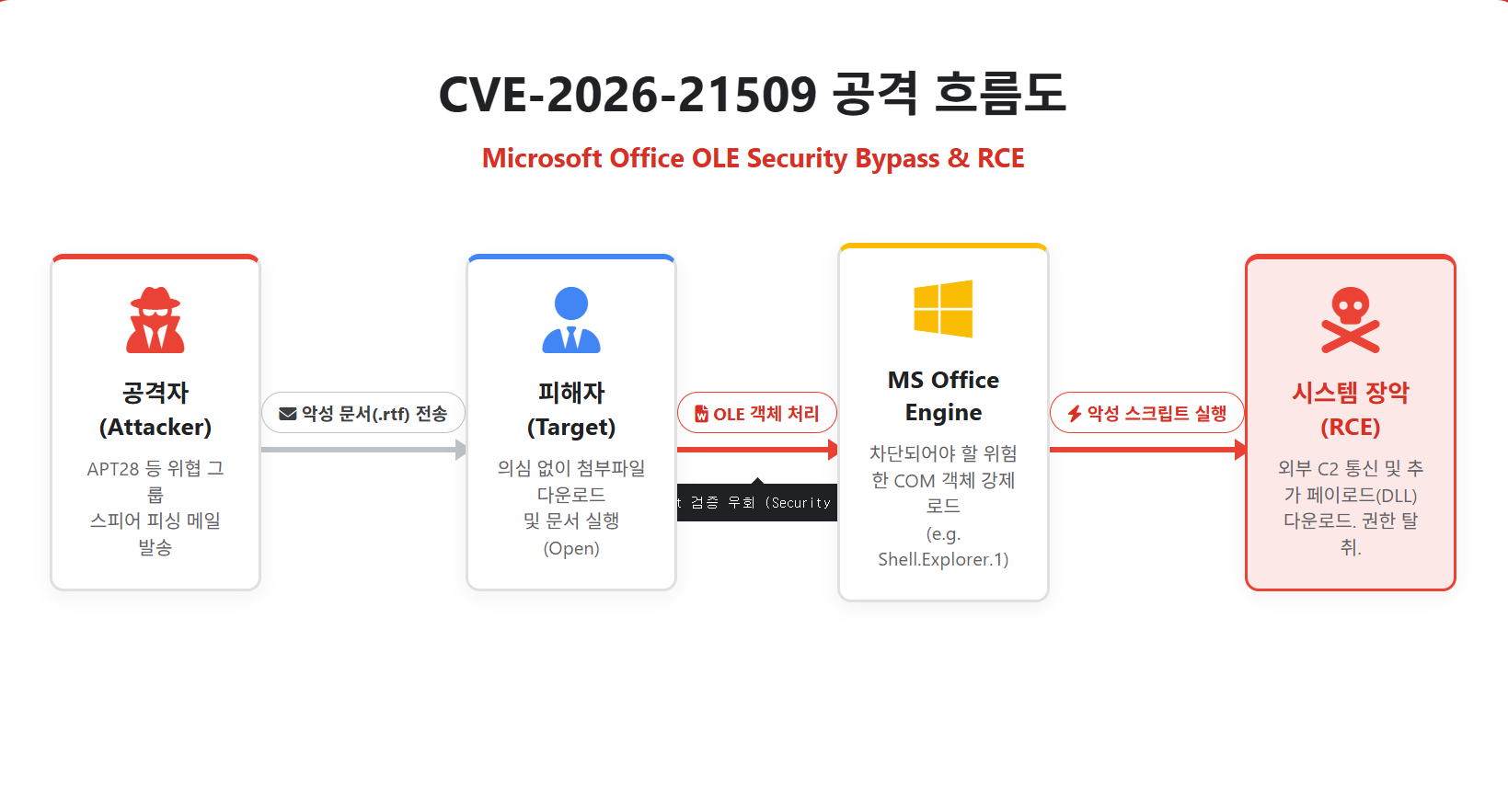
1. Target Selection: Attackers plan spear-phishing email campaigns disguised with enticing subjects (e.g., invoices, HR notices, emergency alerts) that target users are likely to open without suspicion.
2. Malicious Document Delivery: RTF or DOCX files embedded with special payloads that neutralize OLE defenses are attached and sent to target users.
3. Malicious Object Loading: When users download and execute (Open) email attachments, Office forcibly loads dangerous COM objects—originally intended to be blocked—into background memory through the vulnerability.
4. Privilege Acquisition: The loaded malicious objects silently communicate with external C2 (Command and Control) servers to download and execute additional malicious payloads (DLLs, shellcode, etc.), allowing attackers to completely take control of the target endpoint.
through specially crafted documents and execute arbitrary code to completely seize system control.
This vulnerability has an extremely high severity as it enables remote code execution (RCE) simply by victims opening documents in everyday work environments.
Such critical zero-day vulnerabilities can be actively exploited by hacking groups immediately after discovery.
Therefore, organizations using Microsoft Office products must immediately follow these guidelines to secure their systems.
Immediate Patch Application: For Office 2016 and 2019 versions, install the latest Out-of-Band (OOB) emergency security updates distributed by Microsoft to address this vulnerability.
(For Microsoft 365 apps, the fix has been applied on the cloud side, but apps must be fully restarted for the patch to take effect.)
These measures will minimize potential attack risks and strengthen endpoint server and PC security.
CVE-2026-21509 is a critical zero-day vulnerability that allows attackers to completely seize system control
by directly bypassing built-in security mechanisms through the simple action of victims opening manipulated documents.
With confirmed in-the-wild attacks by APT groups and active discussions of detailed analysis and
security bypass techniques, exploitation attempts are expected to surge. Therefore, customers using this product line
must prioritize applying security patches (OOB). Until patches are applied, implement temporary mitigations (registry modifications) or
strictly control access to and execution of suspicious external documents.
Our TA team continuously monitors vulnerabilities discovered in major business software widely used worldwide and
will respond promptly to any newly identified related vulnerabilities in the future.
CVE-2026-21509 is a critical zero-day vulnerability that allows attackers to gain complete control of a system
by simply opening a manipulated document, directly bypassing built-in security measures.
With confirmed cases of in-the-wild attacks by APT groups already underway, and detailed analysis and
security bypass techniques actively discussed, exploitation attempts are expected to surge.
Therefore, customers using this product line should prioritize applying security patches (out-of-box).
Until the patch is applied, they should either apply temporary mitigations (registry modifications) or
strictly control access to and execution of suspicious documents from outside sources.
Our TA team continuously monitors vulnerabilities in major business software widely used worldwide and
will respond promptly to any related vulnerabilities discovered in the future.
1. Overview
Microsoft Office is the most widely used standard business software suite globally by numerous enterprises andorganizations for document creation, data analysis, and communication. To enable seamless document operations and rich content delivery,
Office fundamentally utilizes OLE (Object Linking and Embedding) technology to embed and link data or controls from other applications within documents.
This report provides a technical analysis of CVE-2026-21509, a zero-day vulnerability discovered in the OLE object processing engine and
security mitigation implementation of Microsoft Office. This vulnerability enables arbitrary remote code execution (RCE) by bypassing built-in
security features (such as Kill Bits), has been actively exploited in real-world attacks (in-the-wild) even prior to the official patch release, and
is evaluated as a high-risk security issue with a CVSS v3.1 score of 7.8 (High).

Source : https://thehackernews.com/2026/01/microsoft-issues-emergency-patch-for.html
2. Attack type
CVE-2026-21509 stems from a security validation bypass error that occurswhen Office programs process OLE (Object Linking and Embedding) objects within documents.
The OLE processing engine in Microsoft Office checks security registry settings such as 'Kill Bit' when executing external
objects embedded in documents to block the loading of dangerous COM objects.
In normal logic, malicious scripts or browser controls (e.g., Shell.Explorer.1) should be blocked at this stage,
but vulnerable versions contain a critical flaw that allows attackers to bypass this validation step and forcibly instantiate
objects through specially crafted RTF or Office document structures.
Attackers can execute arbitrary malicious code and seize system control simply by having victims
open manipulated documents (user interaction required), without needing direct system access.
(Note: This vulnerability is not triggered in the Windows Explorer 'Preview Pane'.)
1. Target Selection: Attackers plan spear-phishing email campaigns disguised with enticing subjects (e.g., invoices, HR notices, emergency alerts) that target users are likely to open without suspicion.
2. Malicious Document Delivery: RTF or DOCX files embedded with special payloads that neutralize OLE defenses are attached and sent to target users.
3. Malicious Object Loading: When users download and execute (Open) email attachments, Office forcibly loads dangerous COM objects—originally intended to be blocked—into background memory through the vulnerability.
4. Privilege Acquisition: The loaded malicious objects silently communicate with external C2 (Command and Control) servers to download and execute additional malicious payloads (DLLs, shellcode, etc.), allowing attackers to completely take control of the target endpoint.
3. Response
CVE-2026-21509 discovered in Microsoft Office allows attackers to bypass built-in OLE security features (such as Kill Bits)through specially crafted documents and execute arbitrary code to completely seize system control.
This vulnerability has an extremely high severity as it enables remote code execution (RCE) simply by victims opening documents in everyday work environments.
Such critical zero-day vulnerabilities can be actively exploited by hacking groups immediately after discovery.
Therefore, organizations using Microsoft Office products must immediately follow these guidelines to secure their systems.
Immediate Patch Application: For Office 2016 and 2019 versions, install the latest Out-of-Band (OOB) emergency security updates distributed by Microsoft to address this vulnerability.
(For Microsoft 365 apps, the fix has been applied on the cloud side, but apps must be fully restarted for the patch to take effect.)
These measures will minimize potential attack risks and strengthen endpoint server and PC security.
4. Conclusion
Microsoft Office is an essential business asset that handles core corporate documents and data.CVE-2026-21509 is a critical zero-day vulnerability that allows attackers to completely seize system control
by directly bypassing built-in security mechanisms through the simple action of victims opening manipulated documents.
With confirmed in-the-wild attacks by APT groups and active discussions of detailed analysis and
security bypass techniques, exploitation attempts are expected to surge. Therefore, customers using this product line
must prioritize applying security patches (OOB). Until patches are applied, implement temporary mitigations (registry modifications) or
strictly control access to and execution of suspicious external documents.
Our TA team continuously monitors vulnerabilities discovered in major business software widely used worldwide and
will respond promptly to any newly identified related vulnerabilities in the future.
5. References
- https://thehackernews.com/2026/01/microsoft-issues-emergency-patch-for.html
- https://nvd.nist.gov/vuln/detail/CVE-2026-21509
- https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21509
- https://www.vicarius.io/vsociety/posts/cve-2026-21509-detection-script-microsoft-office-security-feature-bypass-vulnerability