This report provides a technical analysis of the publicly available KillChain project (oxfemale/KillChain),
focusing on how the tool exploits CVE-2026-0828 in Safetica’s vulnerable DLP kernel driver (ProcessMonitorDriver.sys)
to forcibly terminate protected Windows processes (including PPL) and security-related processes.
The scope of analysis includes KillChain’s internal execution flow, vulnerable driver loading,
invocation of the kernel interface through IOCTL 0xB822200C, kernel-side interpretation of user-supplied PID input,
and the exploit path leading to a privileged process termination routine. The report also examines this case as a practical
example of a BYOVD (Bring Your Own Vulnerable Driver) attack, highlighting how abuse of signed vulnerable drivers can lead
to security product neutralization and protection bypass.
It explores the mechanism by which the tool exploits CVE-2026-0828 in Safetica’s vulnerable DLP kernel driver
(ProcessMonitorDriver.sys) to forcibly terminate security processes, including protected Windows processes (PPL).
The scope of analysis includes KillChain’s internal operational structure, the driver loading process, invocation of
the kernel interface via IOCTL 0xB822200C, the kernel-side interpretation of user input (PID), and the exploit path leading
to the process termination routine. Furthermore, this report analyzes the case as a practical example of a BYOVD
(Bring Your Own Vulnerable Driver) attack and examines the security implications of how the abuse of signed vulnerable
drivers can lead to the neutralization of security products and the bypass of protection mechanisms.
A standard mechanism in Windows that allows User-Level applications to communicate directly with Kernel-Level drivers.
What is BYOVD (Bring Your Own Vulnerable Driver)?
An attack technique where an attacker loads a signed but vulnerable driver into the system to gain unauthorized kernel privileges.
The vulnerability stems from a design flaw where the IRP_MJ_DEVICE_CONTROL handler fails to verify the caller's
privileges, passing the PID or process name provided by the user directly into a privileged kernel termination
routine (ZwOpenProcess -> ZwTerminateProcess).
IoValidateDeviceIoControlAccess is the function used to verify the access rights of an IOCTL requestor.
CVE-2026-0828 occurred because ProcessMonitorDriver.sys did not sufficiently apply such authorization checks,
allowing unauthorized users to exploit the exposed IOCTL path to trigger privileged process termination.
The IOCTL 0xB822200C serves as a trigger value that directs the driver to enter its internal process termination
handling branch upon receiving the control code. Subsequently, the driver parses the PID or process name delivered
by the user and passes it to the process termination routine.
The overall flow of a successful attack is outlined below, followed by the actual reproduction steps.
6-1. Environment Information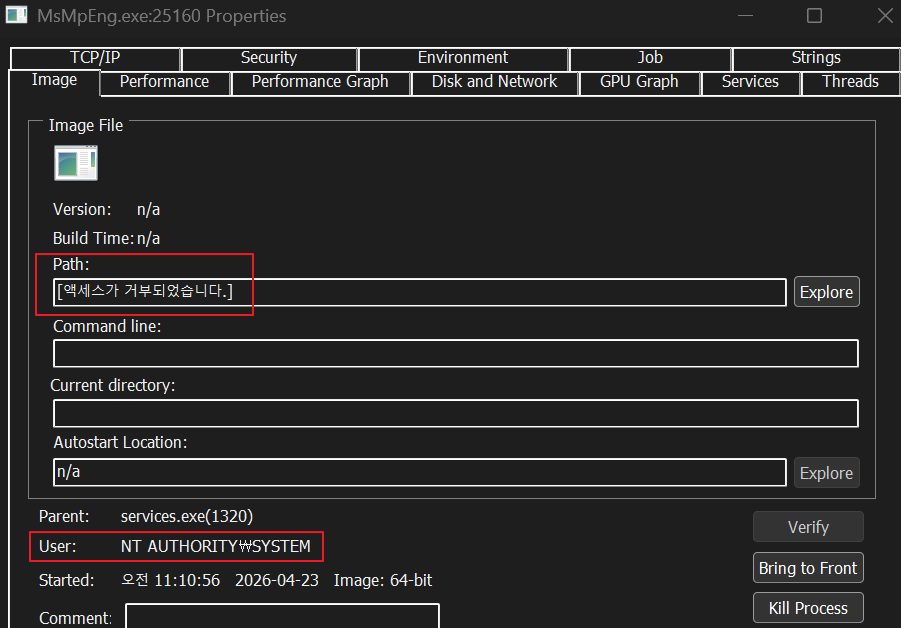
6-2. Reproduction Target
We used Microsoft Defender's MsMpEng.exe as the target process for termination.
As a result of the reproduction, MsMpEng.exe was terminated, and the status "Threat service has stopped"
was confirmed in the Windows Security UI. This confirms that user-mode input is channeled through
the vulnerable driver to a privileged process termination path.
Additionally, we observed that the driver file used in the attack was generated in
the %Temp% directory during the operation.
sys updated to the latest security patch versions. It is essential to update to
the versions recommended by the vendor (11.26.19 or later, 11.29.8 or later, or 10.5.150 or later)
to remove the vulnerable IOCTL path.
General users should enable the Microsoft Vulnerable Driver Blocklist,
Hypervisor-Protected Code Integrity (HVCI), Windows Defender Application Control (WDAC),
and Attack Surface Reduction (ASR) rules—which block the exploitation of known vulnerable
signed drivers—to prevent the introduction and loading of such drivers at the operating system level.
However, since Microsoft’s blocklist does not guarantee the blocking of all vulnerable drivers,
we recommend combining block policies with allowlist-based controls whenever possible.
Monitorapp AIEDR responds to BYOVD attacks and related precursor activities,
such as attempts to load vulnerable drivers, as follows
vulnerable ProcessMonitorDriver.sys driver to obtain kernel-mode process termination primitives
via a BYOVD (Bring Your Own Vulnerable Driver) approach.
The core issue is that the private IOCTL 0xB822200C accepts a PID input delivered via
METHOD_BUFFERED and connects it to a privileged termination routine without sufficient
validation of the caller's privileges.
This implies that even in modern Windows environments, if a signed but vulnerable driver is
introduced and loaded, security products and protected system processes can become targets of
attack. Therefore, the core of an effective defense lies not only in applying vendor patches
but also in concurrently implementing operating system-level BYOVD protection controls,
such as blocklist policies, Hypervisor-Protected Code Integrity (HVCI), Windows Defender
Application Control (WDAC), and Attack Surface Reduction (ASR) rules.
focusing on how the tool exploits CVE-2026-0828 in Safetica’s vulnerable DLP kernel driver (ProcessMonitorDriver.sys)
to forcibly terminate protected Windows processes (including PPL) and security-related processes.
The scope of analysis includes KillChain’s internal execution flow, vulnerable driver loading,
invocation of the kernel interface through IOCTL 0xB822200C, kernel-side interpretation of user-supplied PID input,
and the exploit path leading to a privileged process termination routine. The report also examines this case as a practical
example of a BYOVD (Bring Your Own Vulnerable Driver) attack, highlighting how abuse of signed vulnerable drivers can lead
to security product neutralization and protection bypass.
1. Overview
This report provides a technical analysis of the publicly available KillChain project (oxfemale/KillChain) hosted on GitHub.It explores the mechanism by which the tool exploits CVE-2026-0828 in Safetica’s vulnerable DLP kernel driver
(ProcessMonitorDriver.sys) to forcibly terminate security processes, including protected Windows processes (PPL).
The scope of analysis includes KillChain’s internal operational structure, the driver loading process, invocation of
the kernel interface via IOCTL 0xB822200C, the kernel-side interpretation of user input (PID), and the exploit path leading
to the process termination routine. Furthermore, this report analyzes the case as a practical example of a BYOVD
(Bring Your Own Vulnerable Driver) attack and examines the security implications of how the abuse of signed vulnerable
drivers can lead to the neutralization of security products and the bypass of protection mechanisms.
2. Objectives
- Verification of the KillChain attack tool's internal operation flow.
- Root cause analysis of the abused vulnerable driver and CVE-2026-0828.
- Analysis of input data transmitted in IOCTL communications and the kernel-side interpretation process.
- Reproduction of the BYOVD (Bring Your Own Vulnerable Driver) attack technique.
A standard mechanism in Windows that allows User-Level applications to communicate directly with Kernel-Level drivers.
What is BYOVD (Bring Your Own Vulnerable Driver)?
An attack technique where an attacker loads a signed but vulnerable driver into the system to gain unauthorized kernel privileges.
3. KillChain Tool Configuration
| Item | Details |
| Tool Type | BYOVD-based kernel process termination tool |
| Exploited Driver | Safetica ProcessMonitorDriver.sys |
| Exploited CVE | CVE-2026-0828 (CVSS 8.2 High) |
| Core Primitive | IOCTL 0xB822200C -> Arbitrary process termination with kernel privileges |
| Key Targets | Windows Defender, EDR Agent, protected system processes, etc. |
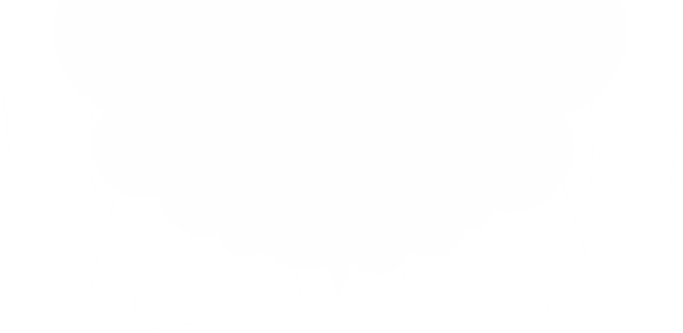
4. KillChain Tool Execution Flow
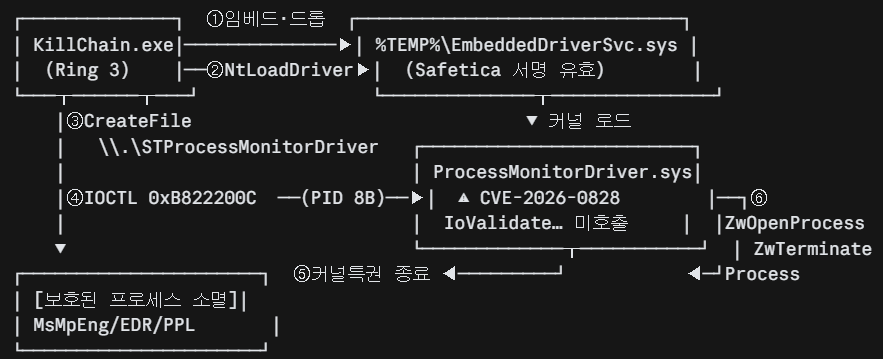
-
- Drop the embedded driver into a temporary folder path.
-
- Load the driver into the kernel using NtLoadDriver.
-
- Obtain a handle to the \\.\STProcessMonitorDriver device using the CreateFile function.
-
- Send the IOCTL 0xB822200C and the target PID to the driver.
-
- The missing validation vulnerability path inside the driver is triggered.
-
- Forcibly terminate the target process in kernel mode.
5. CVE-2026-0828 Vulnerability Summary
| Item | Details |
| CVE ID | CVE-2026-0828 |
| CVSS 3.1 | 8.2 High (`AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:H/A:H`) |
| Publication Date | 2026-01-24 |
| Type | Improper Access Control on IOCTL Handler (CWE-284) |
| Impact | Forced termination of arbitrary processes, including PPL, with standard user privileges |
privileges, passing the PID or process name provided by the user directly into a privileged kernel termination
routine (ZwOpenProcess -> ZwTerminateProcess).
IoValidateDeviceIoControlAccess is the function used to verify the access rights of an IOCTL requestor.
CVE-2026-0828 occurred because ProcessMonitorDriver.sys did not sufficiently apply such authorization checks,
allowing unauthorized users to exploit the exposed IOCTL path to trigger privileged process termination.
The IOCTL 0xB822200C serves as a trigger value that directs the driver to enter its internal process termination
handling branch upon receiving the control code. Subsequently, the driver parses the PID or process name delivered
by the user and passes it to the process termination routine.
6. Attack Success Flow and Reproduction
KillChain.exe (일반 사용자 토큰)
│
│ DeviceIoControl(0xB822200C, &pid=13488, 8)
▼
커널: I/O Manager → IRP 전달
│
▼
ProcessMonitorDriver.DispatchDeviceControl
│ ❌ A. 권한검증 스킵
│ ❌ B. 프로세스 보호등급 검증 스킵
│
│ pid = 13488 (MsMpEng.exe)
▼
ZwOpenProcess(PROCESS_ALL_ACCESS, pid=13488)
│ KernelMode → SeAccessCheck 생략 → hProc 획득
▼
ZwTerminateProcess(hProc, 0)
│ PPL 검사도 KernelMode 경로로 바이패스
▼
MsMpEng.exe 즉시 종료 → Windows Defender 실시간 보호 무력화
The overall flow of a successful attack is outlined below, followed by the actual reproduction steps.
6-1. Environment Information
-
- OS: Windows 11 Pro
-
- Version: 25H2
-
- OS Build: 26200.8246
6-2. Reproduction Target
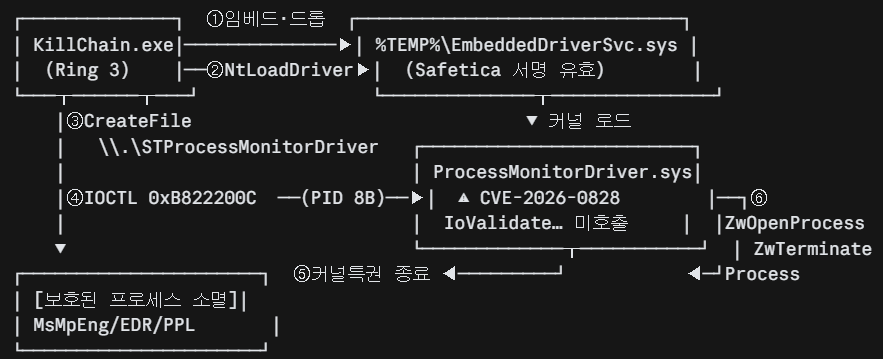
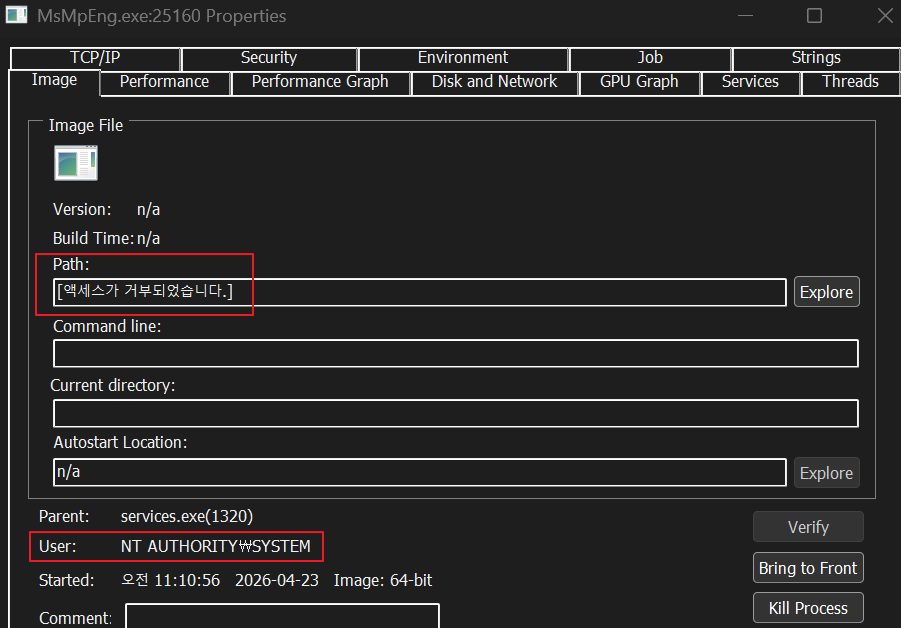
We used Microsoft Defender's MsMpEng.exe as the target process for termination.
- MsMpEng.exe (Antimalware Service Executable)
- A core component of Microsoft Defender that provides real-time malware scanning and system protection in Windows environments.
- By default, it runs with System privileges, preventing users from accessing or modifying process information.
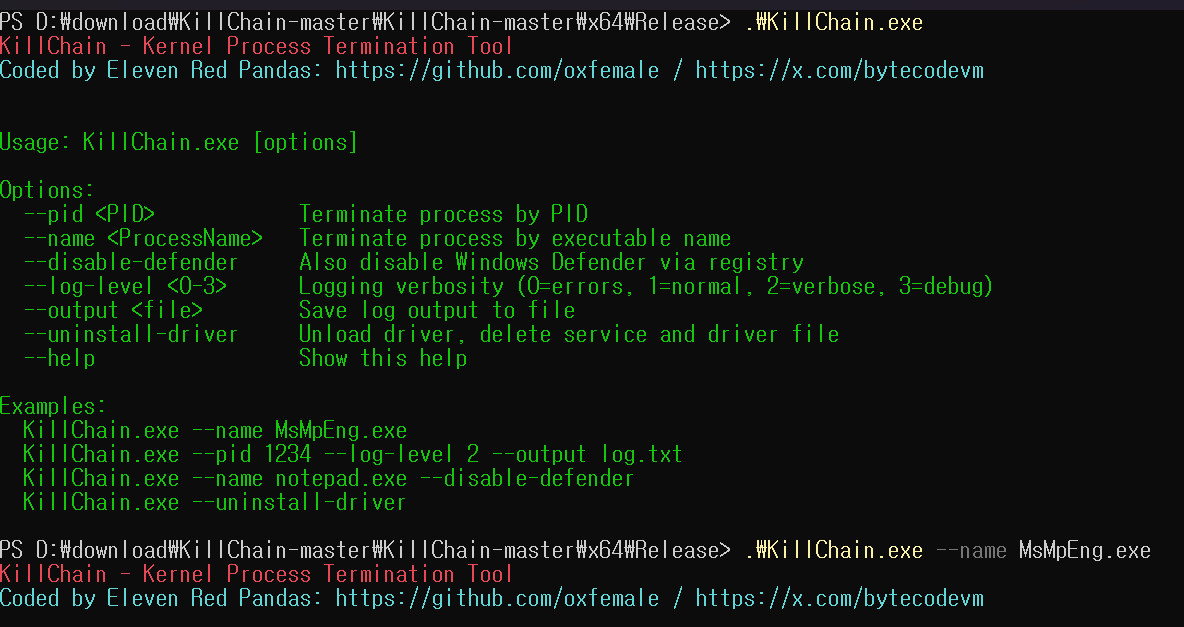
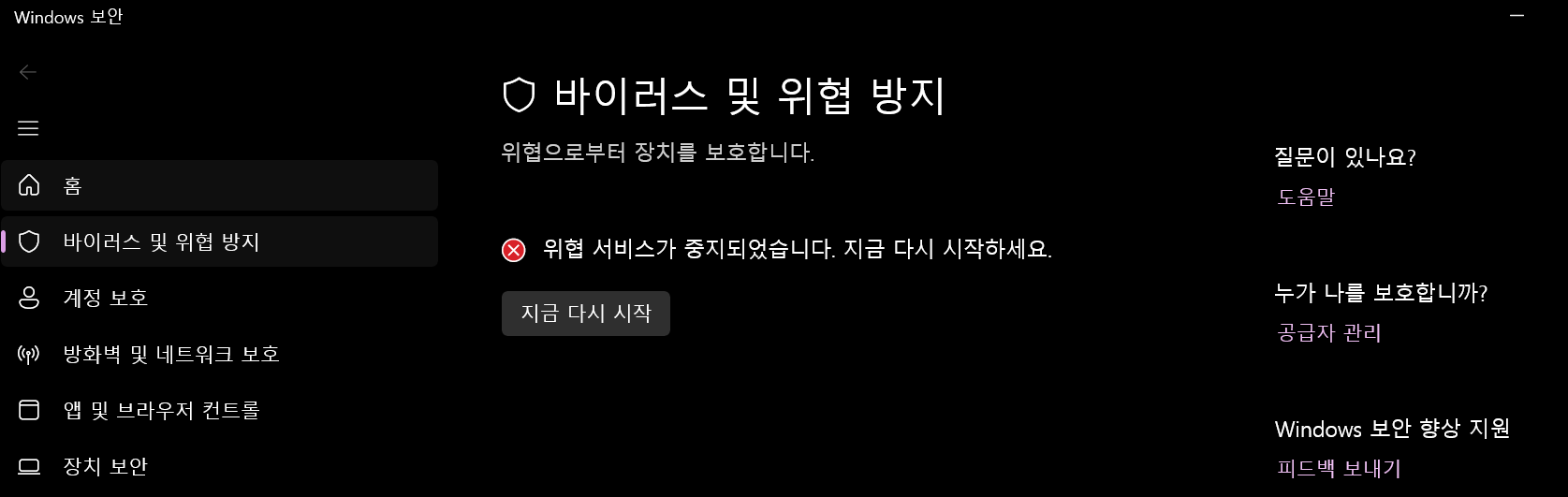
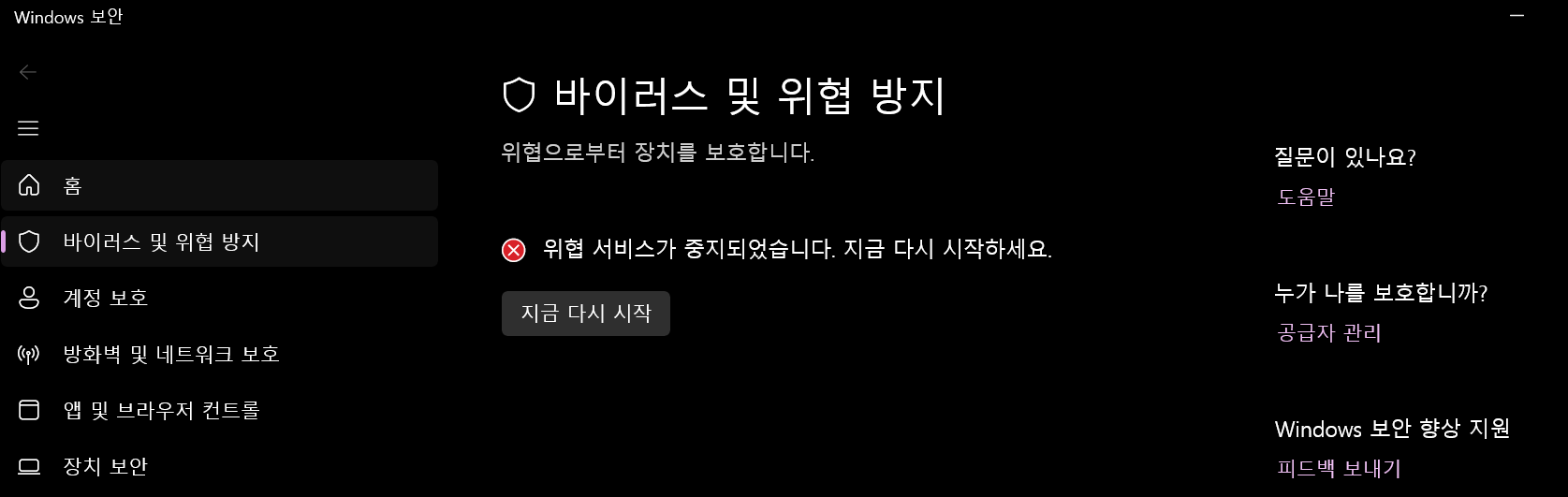
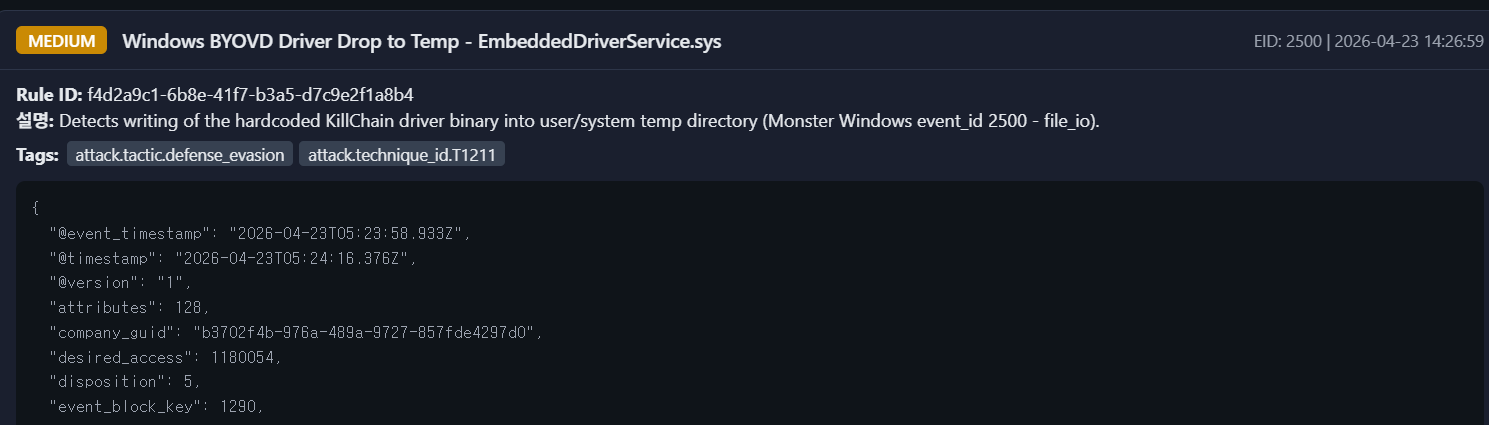
As a result of the reproduction, MsMpEng.exe was terminated, and the status "Threat service has stopped"
was confirmed in the Windows Security UI. This confirms that user-mode input is channeled through
the vulnerable driver to a privileged process termination path.
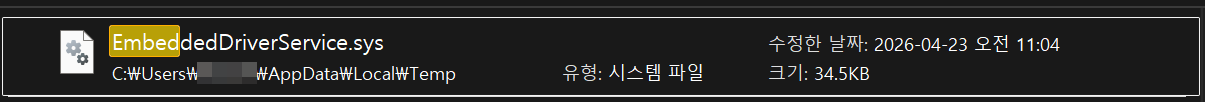
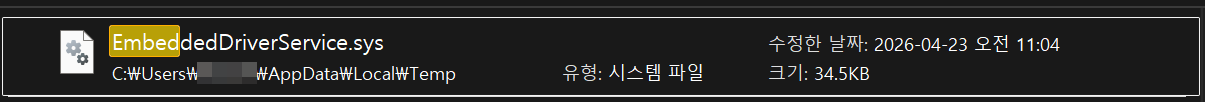
Additionally, we observed that the driver file used in the attack was generated in
the %Temp% directory during the operation.
7. Mitigation
Safetica users must keep clients containing ProcessMonitorDriver.sys updated to the latest security patch versions. It is essential to update to
the versions recommended by the vendor (11.26.19 or later, 11.29.8 or later, or 10.5.150 or later)
to remove the vulnerable IOCTL path.
General users should enable the Microsoft Vulnerable Driver Blocklist,
Hypervisor-Protected Code Integrity (HVCI), Windows Defender Application Control (WDAC),
and Attack Surface Reduction (ASR) rules—which block the exploitation of known vulnerable
signed drivers—to prevent the introduction and loading of such drivers at the operating system level.
However, since Microsoft’s blocklist does not guarantee the blocking of all vulnerable drivers,
we recommend combining block policies with allowlist-based controls whenever possible.
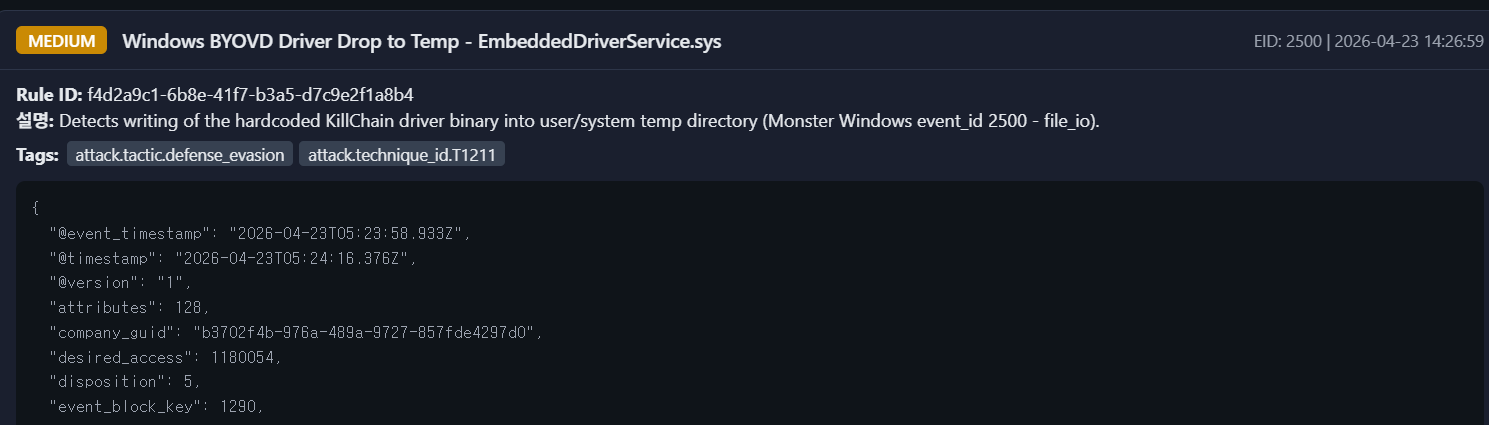
Monitorapp AIEDR responds to BYOVD attacks and related precursor activities,
such as attempts to load vulnerable drivers, as follows
8. Conclusion
This case demonstrates how the publicly available KillChain tool utilizes Safetica’s signed butvulnerable ProcessMonitorDriver.sys driver to obtain kernel-mode process termination primitives
via a BYOVD (Bring Your Own Vulnerable Driver) approach.
The core issue is that the private IOCTL 0xB822200C accepts a PID input delivered via
METHOD_BUFFERED and connects it to a privileged termination routine without sufficient
validation of the caller's privileges.
This implies that even in modern Windows environments, if a signed but vulnerable driver is
introduced and loaded, security products and protected system processes can become targets of
attack. Therefore, the core of an effective defense lies not only in applying vendor patches
but also in concurrently implementing operating system-level BYOVD protection controls,
such as blocklist policies, Hypervisor-Protected Code Integrity (HVCI), Windows Defender
Application Control (WDAC), and Attack Surface Reduction (ASR) rules.