Cisco Integrated Management Controller (IMC) is a critical infrastructure asset that provides out-of-band management for UCS servers.
CVE-2026-20093 is a critical authentication bypass vulnerability that allows a remote, unauthenticated attacker to gain full
administrative access by exploiting a flaw in the password reset logic. With proof-of-concept (PoC) scripts being distributed in
the dark web and a high risk of lateral movement within data centers, immediate action is required. Customers should prioritize
applying the official firmware patches. Until then, external access to the IMC interface must be strictly prohibited,
and AIWAF policies should be deployed to intercept malicious API calls. Our TA team is monitoring exploitation trends against data
center management interfaces and will provide updated detection patterns as new variants emerge.
monitoring, and configuration of Cisco UCS server hardware. It serves a critical security role as it controls essential physical
functions, including server power management, firmware updates, and OS deployment.
This report provides a technical analysis of CVE-2026-20093, an authentication bypass vulnerability discovered
in the Cisco IMC API endpoint. This vulnerability exploits a flaw in the session verification logic, enabling an attacker
to reset administrator passwords or hijack sessions without requiring valid credentials.
It is classified as a top-tier security risk, with a CVSS v3.1 score of 9.8 (Critical).

Source: https://www.cisco.com/site/kr/ko/index.html#tabs-bb2b0d3a0d-item-013f64d475-tab
API endpoints (e.g., /api/v1/password-reset) within the IMC web-based management interface.
The vulnerability occurs because the system processes user-provided input data before verifying the validity of the existing session.
Under normal conditions, every API request must be accompanied by a valid authentication token.
However, in vulnerable versions, a critical flaw exists that allows an attacker to bypass authentication filters and
access internal configuration modification functions directly by sending a specially crafted HTTP POST request.
As long as the attacker has network access to the management interface, they can gain administrative privileges with a single request.
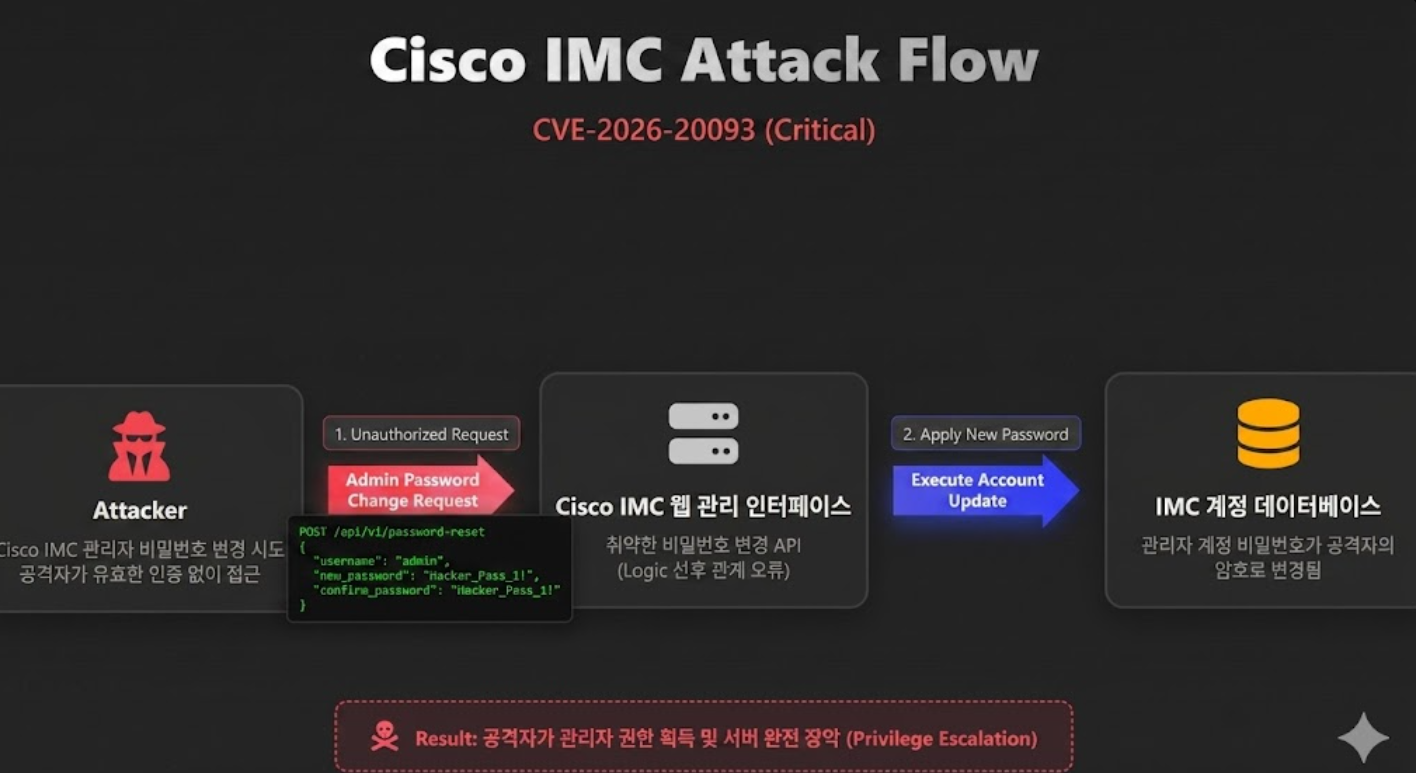
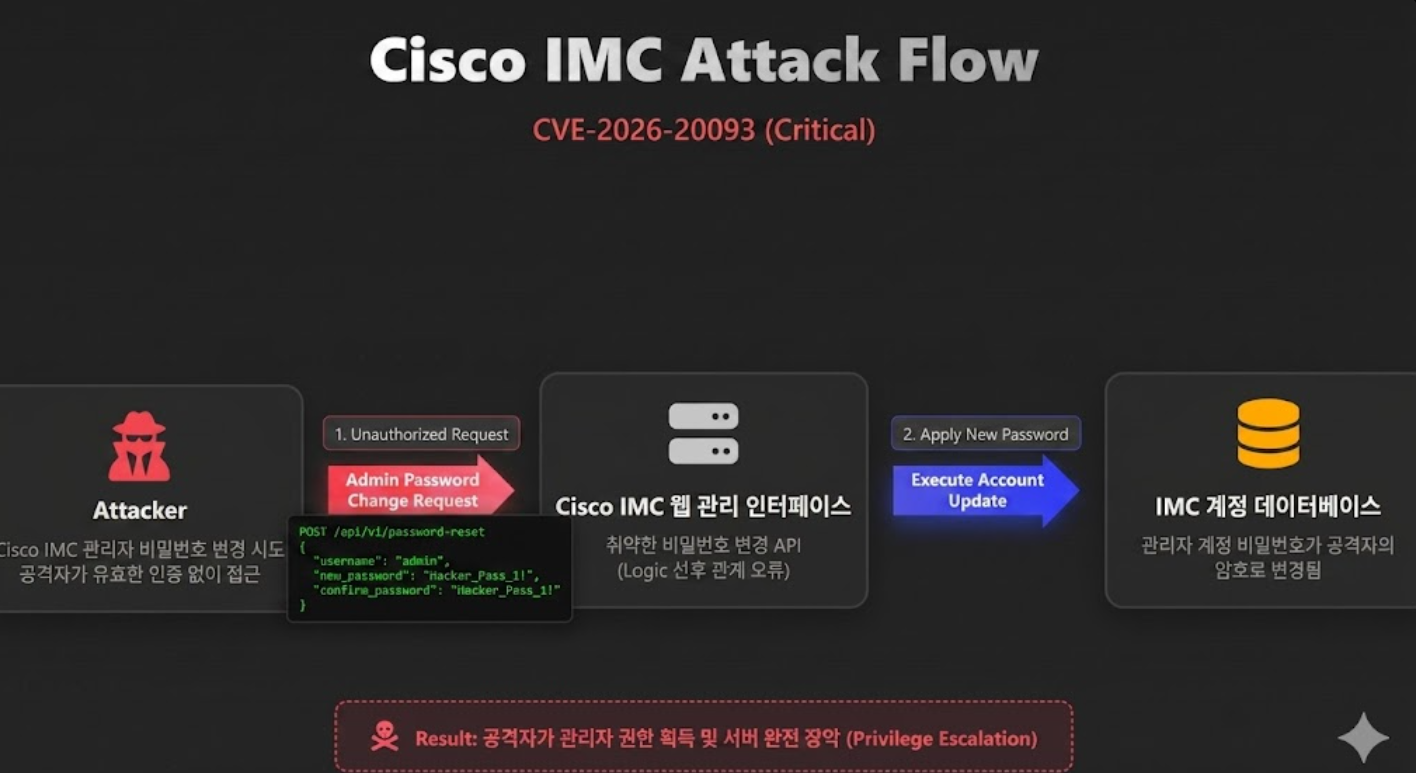
Example Attack Flowchart:
credentials, profoundly impacting the availability and confidentiality of the entire infrastructure.
Given that this vulnerability grants physical-level control over the server, it carries a very high risk of being leveraged
for ransomware deployment or destructive data attacks.
If you are using Cisco products, you must implement the following guidelines immediately
CVE-2026-20093 is a vulnerability that neutralizes the most fundamental defense—authentication—and leaving it unpatched could
create a dire situation where the entire data center becomes a playground for attackers.
Proof-of-Concept (PoC) code has already been made public, and actual exploitation attempts are being detected.
Therefore, customers must prioritize firmware updates above all else. If patching is difficult due to operational constraints,
traffic to the management interface must be strictly monitored and restricted using security appliances such as AIWAF.
Our TA team is focusing on monitoring "authentication bypass" class vulnerabilities in server management solutions and
hardware controllers, and we will continue to respond swiftly through AIWAF pattern optimization.
CVE-2026-20093 is a critical authentication bypass vulnerability that allows a remote, unauthenticated attacker to gain full
administrative access by exploiting a flaw in the password reset logic. With proof-of-concept (PoC) scripts being distributed in
the dark web and a high risk of lateral movement within data centers, immediate action is required. Customers should prioritize
applying the official firmware patches. Until then, external access to the IMC interface must be strictly prohibited,
and AIWAF policies should be deployed to intercept malicious API calls. Our TA team is monitoring exploitation trends against data
center management interfaces and will provide updated detection patterns as new variants emerge.
1. Overview
The Cisco Integrated Management Controller (IMC) is an independent management endpoint designed for the remote administration,monitoring, and configuration of Cisco UCS server hardware. It serves a critical security role as it controls essential physical
functions, including server power management, firmware updates, and OS deployment.
This report provides a technical analysis of CVE-2026-20093, an authentication bypass vulnerability discovered
in the Cisco IMC API endpoint. This vulnerability exploits a flaw in the session verification logic, enabling an attacker
to reset administrator passwords or hijack sessions without requiring valid credentials.
It is classified as a top-tier security risk, with a CVSS v3.1 score of 9.8 (Critical).

Source: https://www.cisco.com/site/kr/ko/index.html#tabs-bb2b0d3a0d-item-013f64d475-tab
2. Attack Type
CVE-2026-20093 is an authentication bypass vulnerability stemming from a logic flaw in the processing of specificAPI endpoints (e.g., /api/v1/password-reset) within the IMC web-based management interface.
The vulnerability occurs because the system processes user-provided input data before verifying the validity of the existing session.
Under normal conditions, every API request must be accompanied by a valid authentication token.
However, in vulnerable versions, a critical flaw exists that allows an attacker to bypass authentication filters and
access internal configuration modification functions directly by sending a specially crafted HTTP POST request.
As long as the attacker has network access to the management interface, they can gain administrative privileges with a single request.
- Target Identification: The attacker uses OSINT tools like Shodan or Censys to identify Cisco IMC management pages exposed to the internet.
- Malicious Request Submission: The attacker sends a JSON payload to the /api/v1/password-reset or /api/v1/account-update endpoint while unauthenticated, designed to modify administrator account information.
- Authentication Bypass: If the request contains specific parameters, the IMC software skips the session verification step and executes the command.
- Privilege Acquisition: The attacker logs in with the newly set password, gaining full control over server hardware (e.g., KVM, virtual media, etc.).
POST /api/v1/password-reset HTTP/1.1
Host: [Target_IMC_IP]
Content-Type: application/json
X-Bypass-Token: True <-- 특정 헤더나 파라미터 조작으로 인증 로직 우회
{
"username": "admin",
"new_password": "Attacker_Password_123!",
"confirm_password": "Attacker_Password_123!"
}
Example Attack Flowchart:
3. Mitigation
The CVE-2026-20093 vulnerability in Cisco IMC allows attackers to gain full control of the system without administratorcredentials, profoundly impacting the availability and confidentiality of the entire infrastructure.
Given that this vulnerability grants physical-level control over the server, it carries a very high risk of being leveraged
for ransomware deployment or destructive data attacks.
If you are using Cisco products, you must implement the following guidelines immediately
- Apply Patches Immediately: Update firmware to the latest release provided by Cisco (IMC Software 4.2(3j) or later, or 4.3(2b) or later).
- Network Isolation: Ensure the IMC management interface is not exposed to the public internet. Implement Access Control Lists (ACLs) to ensure access is restricted to internal management VPNs or dedicated Out-of-Band (OOB) management networks.
-
AIWAF Response: The AIWAF team is currently analyzing abnormal API call patterns associated with this vulnerability.
- Pattern Detection: Implement custom rules to immediately block unauthorized POST requests and specific parameters attempting to bypass authentication on the /api/v1/ path.
- Prevent False Positives: We recommend whitelisting IP addresses of legitimate administrators and configuring alerts to detect any account modification attempts originating from non-authorized IPs.
4. Conclusion
The Cisco IMC is a critical asset that controls the servers forming the foundation of enterprise infrastructure.CVE-2026-20093 is a vulnerability that neutralizes the most fundamental defense—authentication—and leaving it unpatched could
create a dire situation where the entire data center becomes a playground for attackers.
Proof-of-Concept (PoC) code has already been made public, and actual exploitation attempts are being detected.
Therefore, customers must prioritize firmware updates above all else. If patching is difficult due to operational constraints,
traffic to the management interface must be strictly monitored and restricted using security appliances such as AIWAF.
Our TA team is focusing on monitoring "authentication bypass" class vulnerabilities in server management solutions and
hardware controllers, and we will continue to respond swiftly through AIWAF pattern optimization.