This vulnerability is a supply chain attack discovered in Aqua Security's Trivy.
It allows an attacker to obtain an account with write permissions for tags within the open source code and
link commits containing malicious code to most version tags, thereby executing Trivy containing the malicious code.
Regarding this vulnerability, Trivy has redeployed the relevant release versions and recommends updating
to v0.69.2 and v0.69.3, which have been verified as safe.
file systems, Git repositories, and Kubernetes environments. It is primarily used to perform security checks within CI/CD pipelines.
This report summarizes an analysis of the CVE-2026-33634 vulnerability identified in the service.

Source: https://trivy.dev/
It allows an attacker to insert malicious code into the scanner’s official releases, leading to the execution of
that code within services that utilize the affected scanner.
An attacker operating under the name “TeamPCP” confirmed that access obtained from a credential compromise incident
in March was still valid. Using these credentials, the attacker gained access to an account with tag write permissions
in the open-source repository. Through this account, the attacker pushed new commits containing malicious code and used
the force-updating tag feature to make existing release versions point to the malicious commits.
During this process, the attacker manipulated commit metadata to impersonate an Aqua Security engineer,
making the changes appear legitimate. As most version tags were redirected to the malicious commits,
even users relying on specific tagged versions inadvertently downloaded and executed the compromised code.
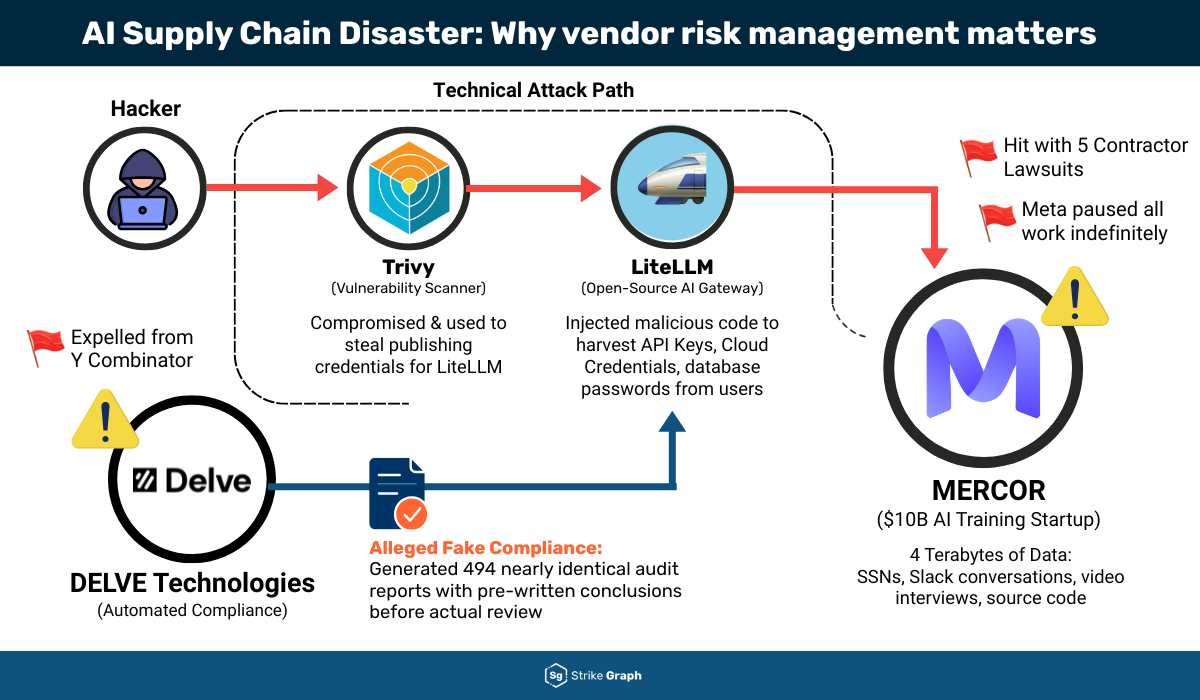
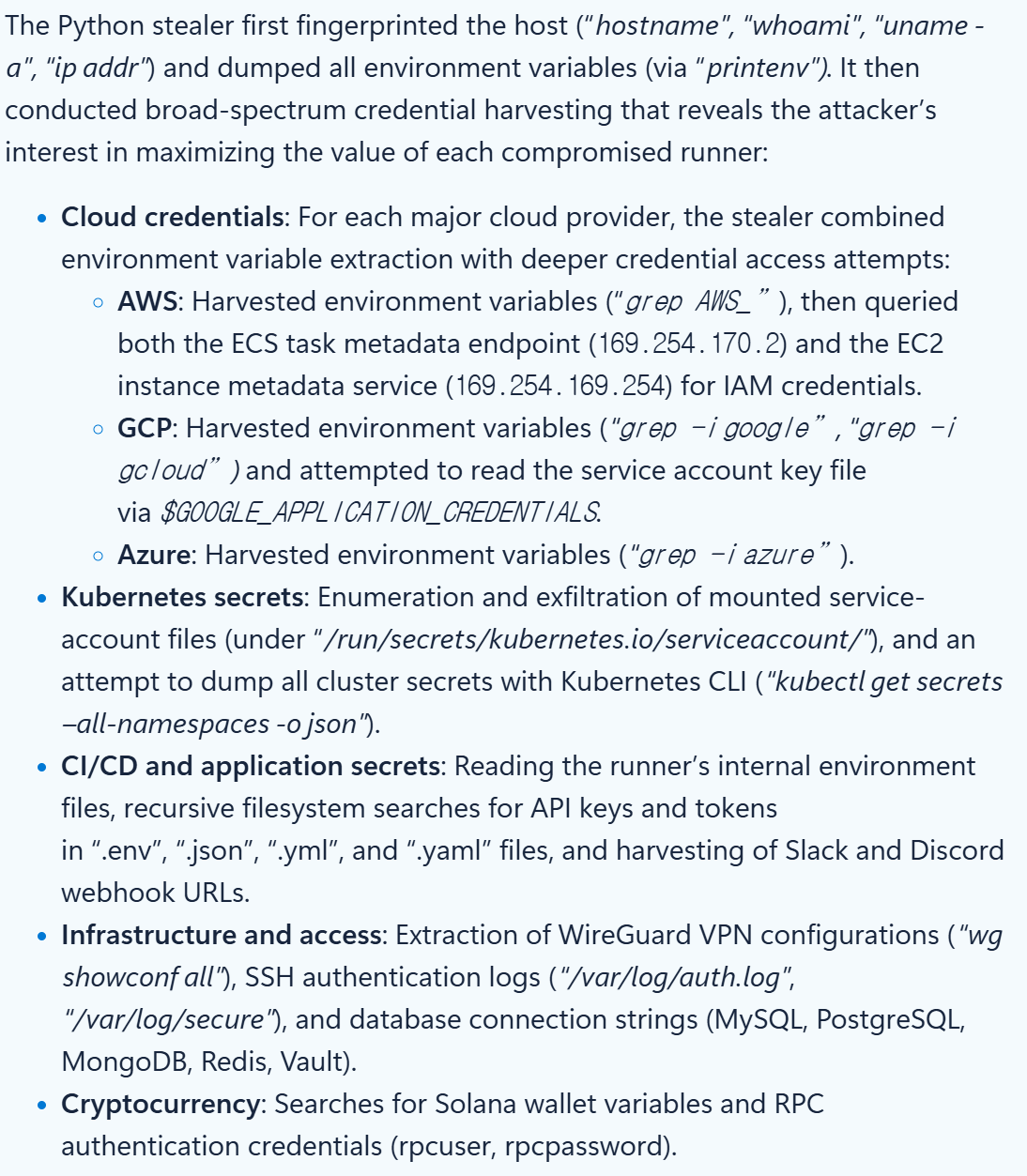
The malicious code initially scans for all running GitHub Actions processes, extracts environment variable values from those processes,
and uses them to exfiltrate sensitive information from the file system, including credentials such as GitHub tokens and cloud service credentials.
Based on the exfiltrated data, the attacker attempted further exploitation, including launching additional attacks and establishing persistent backdoors.
Source: https://www.microsoft.com/en-us/security/blog/2026/03/24/detecting-investigating-defending-against-trivy-supply-chain-compromise/
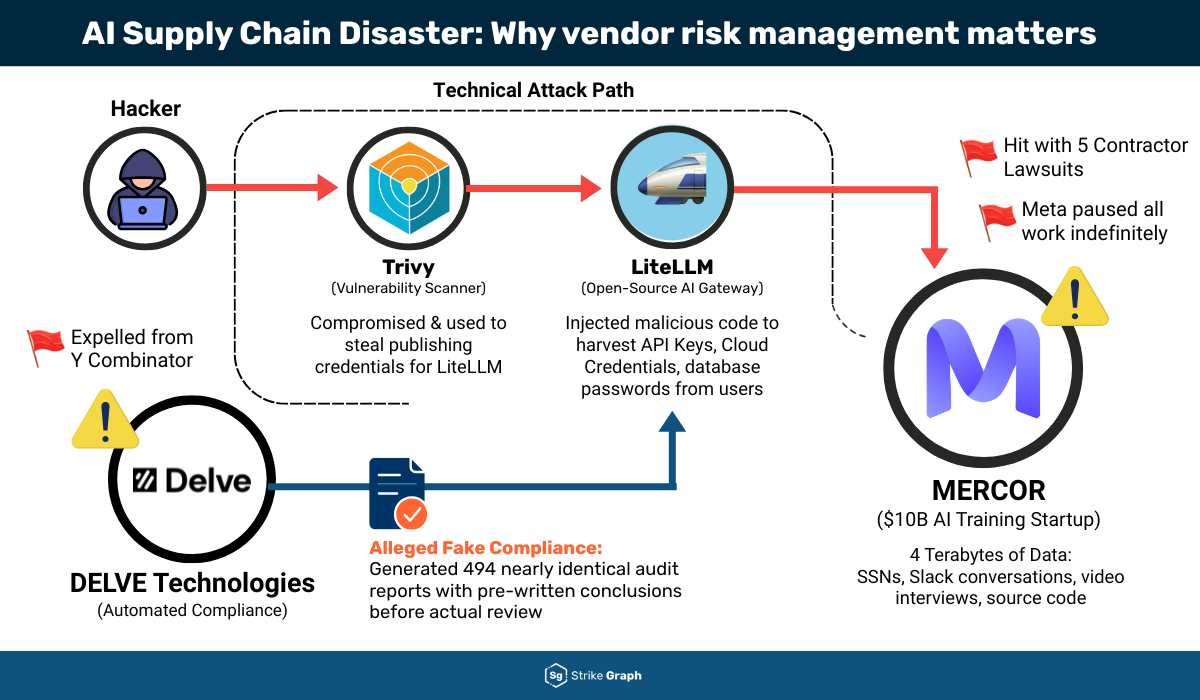
In the case of the open-source AI gateway service LiteLLM, the supply chain attack led to the leakage of the PYPI_PUBLISH token.
The attacker exploited this token to create a malicious version of LiteLLM, which was subsequently uploaded to PyPI.
Source: https://www.strikegraph.com/blog/the-mercor-breach-exposed-silicon-valleys-fragile-ai-supply-chain
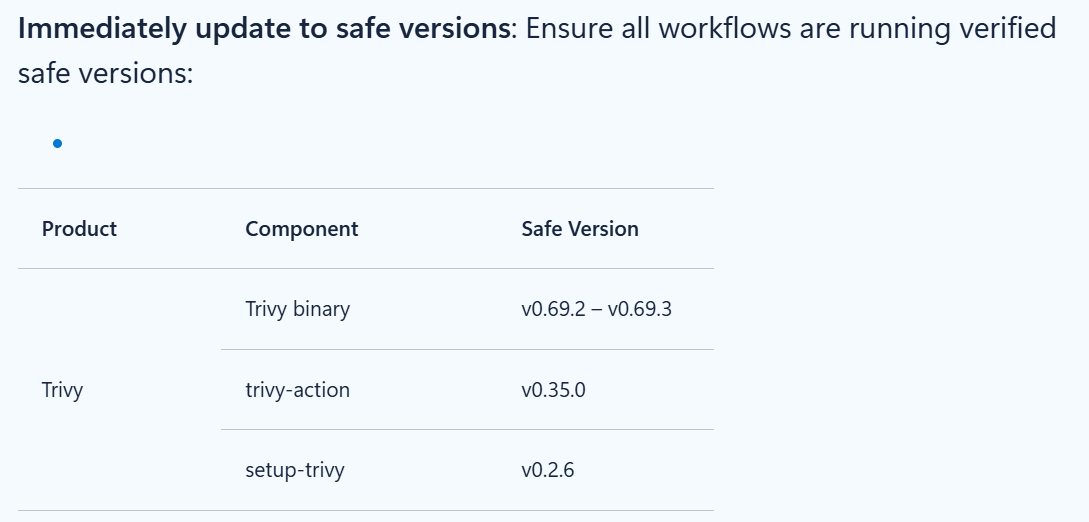
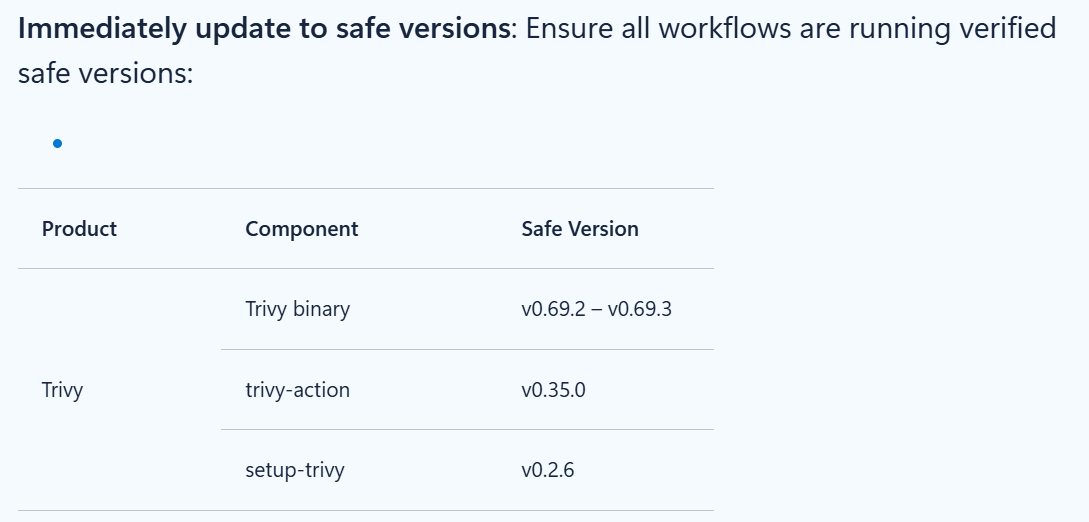
Aqua Security republished 74 release versions on March 20.
Accordingly, organizations using the affected service should update to the verified safe versions, v0.69.2 or v0.69.3,
or mitigate the risk by pinning GitHub Actions version tags to specific SHA hashes.
Source: https://www.microsoft.com/en-us/security/blog/2026/03/24/detecting-investigating-defending-against-trivy-supply-chain-compromise/
The CVE-2026-33634 vulnerability identified in this service has a significant impact. As it executes automatically within GitHub environments,
malicious activities are difficult to detect promptly, making this vulnerability particularly challenging to respond to.
Therefore, organizations using this service should promptly apply security measures such as updating to verified safe versions
and pinning dependencies to specific SHA hashes.
Our TA team is actively monitoring supply chain attacks targeting Trivy and other open-source projects,
and we will continue to respond swiftly to any related vulnerabilities identified in the future.
It allows an attacker to obtain an account with write permissions for tags within the open source code and
link commits containing malicious code to most version tags, thereby executing Trivy containing the malicious code.
Regarding this vulnerability, Trivy has redeployed the relevant release versions and recommends updating
to v0.69.2 and v0.69.3, which have been verified as safe.
1. Overview
Aqua Security's Trivy is an open-source vulnerability scanner that detects security issues in Docker container images,file systems, Git repositories, and Kubernetes environments. It is primarily used to perform security checks within CI/CD pipelines.
This report summarizes an analysis of the CVE-2026-33634 vulnerability identified in the service.

Source: https://trivy.dev/
2. Attack Type
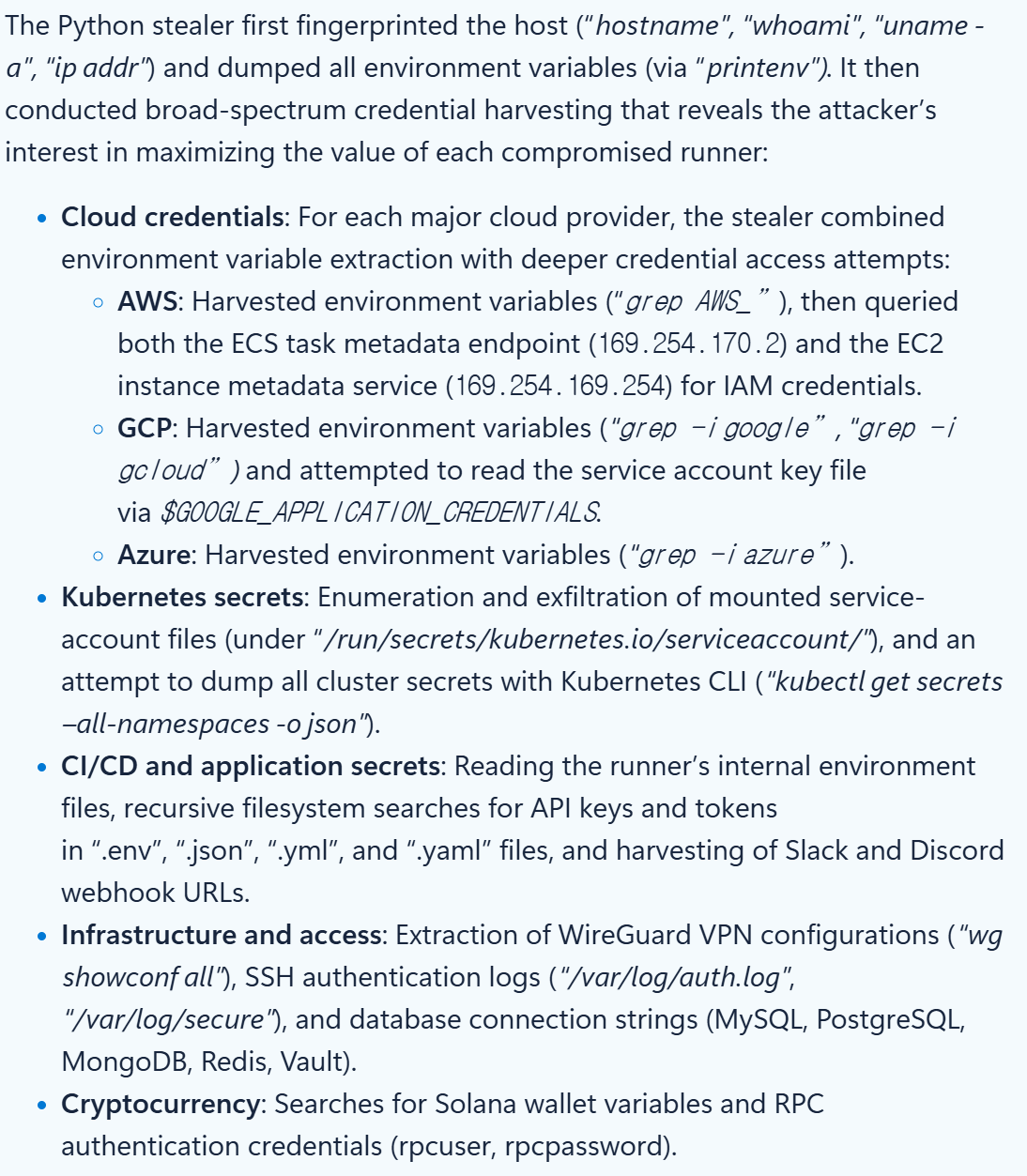
The CVE-2026-33634 vulnerability is a supply chain attack identified in Trivy.It allows an attacker to insert malicious code into the scanner’s official releases, leading to the execution of
that code within services that utilize the affected scanner.
An attacker operating under the name “TeamPCP” confirmed that access obtained from a credential compromise incident
in March was still valid. Using these credentials, the attacker gained access to an account with tag write permissions
in the open-source repository. Through this account, the attacker pushed new commits containing malicious code and used
the force-updating tag feature to make existing release versions point to the malicious commits.
During this process, the attacker manipulated commit metadata to impersonate an Aqua Security engineer,
making the changes appear legitimate. As most version tags were redirected to the malicious commits,
even users relying on specific tagged versions inadvertently downloaded and executed the compromised code.
The malicious code initially scans for all running GitHub Actions processes, extracts environment variable values from those processes,
and uses them to exfiltrate sensitive information from the file system, including credentials such as GitHub tokens and cloud service credentials.
Based on the exfiltrated data, the attacker attempted further exploitation, including launching additional attacks and establishing persistent backdoors.
Source: https://www.microsoft.com/en-us/security/blog/2026/03/24/detecting-investigating-defending-against-trivy-supply-chain-compromise/
In the case of the open-source AI gateway service LiteLLM, the supply chain attack led to the leakage of the PYPI_PUBLISH token.
The attacker exploited this token to create a malicious version of LiteLLM, which was subsequently uploaded to PyPI.
Source: https://www.strikegraph.com/blog/the-mercor-breach-exposed-silicon-valleys-fragile-ai-supply-chain
3. Mitigation
The supply chain attack exposure window was from March 19, 2026, 17:43 (UTC) to March 20, 2026, 05:40 (UTC).Aqua Security republished 74 release versions on March 20.
Accordingly, organizations using the affected service should update to the verified safe versions, v0.69.2 or v0.69.3,
or mitigate the risk by pinning GitHub Actions version tags to specific SHA hashes.
Source: https://www.microsoft.com/en-us/security/blog/2026/03/24/detecting-investigating-defending-against-trivy-supply-chain-compromise/
4. Conclusion
Trivy is an open-source vulnerability scanner primarily used to perform security checks within CI/CD pipelines.The CVE-2026-33634 vulnerability identified in this service has a significant impact. As it executes automatically within GitHub environments,
malicious activities are difficult to detect promptly, making this vulnerability particularly challenging to respond to.
Therefore, organizations using this service should promptly apply security measures such as updating to verified safe versions
and pinning dependencies to specific SHA hashes.
Our TA team is actively monitoring supply chain attacks targeting Trivy and other open-source projects,
and we will continue to respond swiftly to any related vulnerabilities identified in the future.
5. References
- https://nvd.nist.gov/vuln/detail/CVE-2026-33634
- https://rosesecurity.dev/2026/03/20/typosquatting-trivy.html
- https://www.wiz.io/blog/trivy-compromised-teampcp-supply-chain-attack
- https://www.microsoft.com/en-us/security/blog/2026/03/24/detecting-investigating-defending-against-trivy-supply-chain-compromise/